Merchant-based money laundering Part 1: Phantom Shipments
First in a three-part series
By Keith Furst
Founder of Data Derivatives
A boutique consulting firm focused on financial crimes technology.
September 8, 2016
kfurst@dataderivatives.com
With editing and a brief introduction by Brian Monroe, Director of Content and Business Development at ACFCS
This is an important story looking at the creativity of criminal networks in attempting to use credit cards, rather than cash deposits, wires or ACH transactions, in laundering their illicit proceeds and moving value across international borders while hopefully evading the transactional scrutiny of ever-more aggressive anti-money laundering (AML) teams.
This is a key development for financial crime compliance teams to be aware of because, though they may be very attuned to suspicious or aberrant activity tied possible money laundering, and in tandem, well-versed in the classic red flags of credit card fraud, AML analysts may not be looking at credit card transactions as a means to launder ill-gotten gains.
With that in mind, it would behoove banks with oversight responsibility of certain credit card relationships – and potentially related third-party payment processors and the merchant acquirers themselves, even those not subject to formal AML obligations – to start looking at credit card transactions and asking many of the same questions about if the activity could be a red flag for money laundering or the foundation of a suspicious activity report.
Editor's Note: This article originally appeared on the Association of Certified Financial Crime Specialists on September 8, 2016.
This is an important story looking at the creativity of criminal networks in attempting to use credit cards, rather than cash deposits, wires or ACH transactions, in laundering their illicit proceeds and moving value across international borders while hopefully evading the transactional scrutiny of ever-more aggressive anti-money laundering (AML) teams.
This is a key development for financial crime compliance teams to be aware of because, though they may be very attuned to suspicious or aberrant activity tied possible money laundering, and in tandem, well-versed in the classic red flags of credit card fraud, AML analysts may not be looking at credit card transactions as a means to launder ill-gotten gains.
With that in mind, it would behoove banks with oversight responsibility of certain credit card relationships – and potentially related third-party payment processors and the merchant acquirers themselves, even those not subject to formal AML obligations – to start looking at credit card transactions and asking many of the same questions about if the activity could be a red flag for money laundering or the foundation of a suspicious activity report.
That would include things like:
- Do the credit card transactions make sense or a marked change, in terms of amounts, customers or items, from historical practices?
- Why is the merchant going international when they could get the same items domestically?
- Why is the merchant using credit cards for large transactions involving items they normally wouldn’t buy or sell, such as a fruit seller purchasing high-end electronics?
- Is there any hard evidence that, even though a payment was made, that an item was actually shipped?
“The reality is that merchant acquirers don’t have the same BSA/AML requirements of banks, but this doesn’t mean that if there is a valid money laundering typology that they shouldn’t collect their own intelligence,” Furst said.
This piece is a great read done for the best reason of all: to share information and insight with the broader financial crime and compliance community. Enjoy.
Transnational organized crime (TOC) groups have dealt with the perennial problem of moving value across borders undetected.
At some point all of these groups deal with the three steps in the money laundering process, but the first one, placement, is potentially the most hazardous hurdle to overcome. TOCs ship drugs to the United States via various means and have their major distribution hubs sell the drugs to other dealers.
The investigative journalist and author Patrick Radden Keefe gives an interesting account of the credit-based system in the drug trafficking trade in his New York Times article “Cocaine Incorporated,” which supports the assertion that cash generated in the United States must be laundered or smuggled back to Mexico.
“As preferred customers, they often took Chapo’s drugs without putting any money down, then paid the cartel only after they sold the product. This might seem unlikely, given the pervasive distrust in the underworld, but the narcotics trade is based on a robust and surprisingly reliable system of credit. In a sense, a cartel like Sinaloa has no choice but to offer a financing option, because few wholesale buyers have the liquidity to pay cash upfront for a ton of cocaine. “They have to offer lines of credit,” Wardrop told me, “no different from Walmart or Sears.” This credit system, known as “fronting,” rests on an ironclad assumption that in the American marketplace, even an idiot salesman should have no trouble selling drugs.”
But how do the cartels get the cash generated from drug deals which occurred on United States soil back into their possession?
There are several methods to achieve this, but the purpose of this article is to explore another possible way to move value across borders which can be coined as “merchant-based money laundering.”
The growth of credit cards for business-to-business (B2B) payments
Businesses in the United States are continuing to increase their use of corporate credit cards for business-to-business (B2B) payments. According to a payments study “spending increased 25 percent – from $196 billion to $245 billion – and is forecast to continue increasing at a rate of around 10 percent – through 2018.”
As well, many business credit cards offer attractive cash back reward programs so businesses are opting to pay their suppliers with a company credit card as opposed to an Automated Clearing House (ACH) transfer, check or wire.
Additionally, it is becoming more common for a business to use a company credit card to make a purchase of goods or services for tens of thousands of dollars in a single transaction.
What is a merchant?
A merchant can be defined as any business which accepts credit, debit, prepaid or gift cards as a form of payment with the assistance of a merchant acquirer. Click here to read more about merchant acquiring.
What is merchant-based money laundering?
Merchant-based money laundering can be defined as the process where goods and/or services are purchased by an individual or company from a merchant, but the goods or services are undervalued or not actually provided at all.
If the goods associated with the transaction were never actually shipped, then this could be categorized as a “phantom shipment.”
Merchant-based money laundering red flags
One example of merchant-based money laundering would be a cash-intensive business, such as a privately-owned supermarket located in the United States using a company credit card to make a high value purchase of goods from a Mexican merchant.
If the supermarket makes high-value purchases from the Mexican merchant on a regular basis, then it should be considered suspicious if one or more of the following criteria are met:
- The goods purchased are not likely to be resold in a supermarket, i.e. high end electronics, jewelry, etc.
- It’s possible to purchase similar products at comparable prices from another merchant located within the United States.
- The supermarket doesn’t usually use its company credit card to purchase other items it routinely sells, i.e. meat, produce, dairy, etc.
The below graphic shows some common cash-intensive business examples, but this list is not all inclusive. Click here to read more on cash-intensive businesses
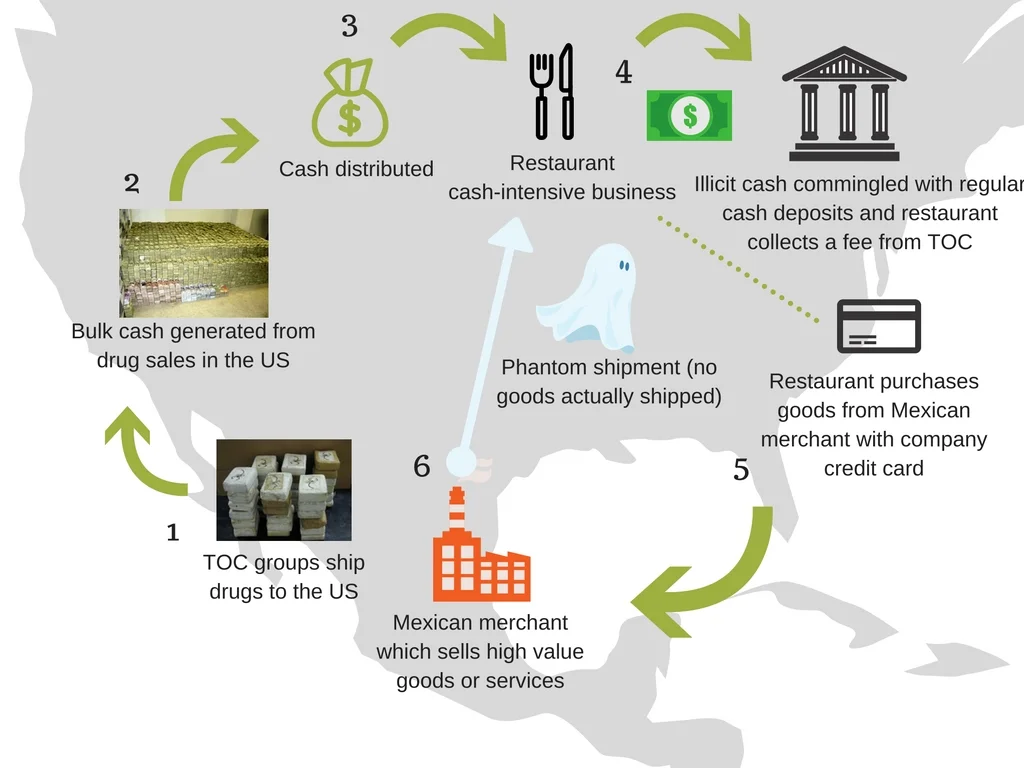
What would merchant-based money laundering look like?
Merchant-based money laundering would typically follow this high-level flow:
- TOC groups ship drugs to the US: This step assumes that the TOC will ship drugs on credit and collect the cash at some point in the future. Additionally, the TOCs usually have their own people reselling the drugs to other dealers in the US.
- Bulk cash generated from drug sales: The TOC’s representatives sell the drugs to other dealers and now have a lot of cash which must be laundered or shipped in bulk back to Mexico.
- Cash distributed: The TOC’s representatives in the US use their local connections to form a network of alliances with cash-intensive businesses in the area where the group operates. The cash-intensive businesses are persuaded with a fee or are coerced into receiving regular deliveries of cash.
- Illicit cash commingled with regular cash deposits and restaurant collects a fee from TOC: The cash-intensive business takes the cash delivery from the TOC and deposits it with the company’s regular cash deposits over a period of time. The cash-intensive business is able to collect a fee for each cash delivery.
- Restaurant purchases goods from Mexican merchant with company credit card: The cash-intensive business is instructed by the TOC to make regular purchases from specific merchants located in Mexico on a regular basis.
- Phantom shipment (no goods actually shipped): The Mexican merchant receives the order from the cash-intensive business located in the United States. However, since the TOC has instructed both the cash-intensive business and the Mexican merchant of the process, no goods are actually shipped.
The above graphic simply illustrates that there are other innovative ways for TOCs to transfer value across borders.
The money laundering process doesn’t stop with the Mexican merchant, but the TOCs successfully passed the first step in the money laundering process by distributing cash to various businesses by converting cash deliveries into a bank deposit through the use of business credit cards.
I’m not a bank
The merchant acquirer processes the payments, but the merchant’s bank is the institution that deposits the money into the merchant’s account, so the acquirer could see itself more as a processing agent than a financial institution.
To a certain extent this is true, but the merchant acquirer will have access to data that the merchant’s bank won’t have and this data could contain money laundering typologies which should be monitored more closely. The merchant acquirer also tends to be more focused on chargebacks because this is the financial exposure of the acquirer and what could lead to a loss.
Why go to all of this trouble?
Some may be asking themselves why would the TOCs go to all of this trouble to launder their money through a merchant when they can simply have the U.S.-based cash-intensive business send a wire to Mexico?
This is a valid objection, but one way to think about the benefits of merchant-based money laundering to the TOCs, as opposed to simply sending international wires, is the level of risk associated with each type of transaction from a financial institution’s point of view.
Most financial institutions will categorize international wires as high-risk, but credit card and merchant acquiring activity will not fall into the same anti-money laundering (AML) risk category.
- If you were planning to drive a sports car over the speed limit, would you drive on a road where you knew the police were waiting with their radar guns or would you take a back road which was not as heavily policed?
So what now?
Merchant acquirers and credit card companies should be aware that TOCs and other criminal groups can use their financial products to move value across borders. While the cash is still being deposited into a bank account the merchant acquirer and credit card company will have access to data that the merchant’s bank doesn’t. If a business’ cash deposits increases how could the bank determine that the increase was generated from illicit sources as opposed to legitimate business revenue? The answer is that they can’t. The red flags may only be contained in the business’ credit card activity and with the merchant acquirer and only then will it become clear that the high value credit card purchases didn’t make business sense.
How Data Scientists & Compliance Can Work Together Better: Keith Furst Explains
Keith Furst and I discuss how data scientists working on compliance projects can work together better to avoid unintended consequences which prevent compliance from getting the data it needs.
Keith Furst and I discuss how data scientists working on compliance projects can work together better to avoid unintended consequences which prevent compliance from getting the data it needs.
3 things we learned at our Fintech Talks - July Edition Dinner Event
Last Thursday we had the privilege of hosting 30 senior banking executives at our quarterly FinTech Talks dinner event. The event theme was Trust, Transaction Monitoring and AML for financial messaging, and Keith Furst, a financial crime expert with experience at leading European and American financial institutions flew in from New York to headline the discussion.
Last Thursday we had the privilege of hosting 30 senior banking executives at our quarterly FinTech Talks dinner event. The event theme was Trust, Transaction Monitoring and AML for financial messaging, and Keith Furst, a financial crime expert with experience at leading European and American financial institutions flew in from New York to headline the discussion. Keith took our guests on a journey from past, to present and the possible future of AML mechanisms, correspondent banking, and explored the challenges associated with monitoring potentially fraudulent activity.
Click here to read about the full event details
Why Banks Must Evolve their AML Process to Manage Micro-Jurisdictional Risk
United States sanctions policies have evolved over the years, from country-wide embargos to more nuanced approaches targeting specific entities. According to Jacob J. Lew, Secretary of the Treasury, the sanctions implemented today are more focused on bad actors while trying to limit the negative externalities. Lew described his view on the traditional sanctions model at the Carnegie Endowment for International Peace which is eloquently summarized by this quote:
The Evolution of Sanctions
United States sanctions policies have evolved over the years, from country-wide embargos to more nuanced approaches targeting specific entities. According to Jacob J. Lew, Secretary of the Treasury, the sanctions implemented today are more focused on bad actors while trying to limit the negative externalities. Lew described his view on the traditional sanctions model at the Carnegie Endowment for International Peace which is eloquently summarized by this quote:
Lew went on to describe how the application of sanctions has evolved over the years, and through better financial intelligence, strategy, and design, the new model can home in directly on bad actors:
The Evolution of US Trade Sanctions
The diagram below illustrates the evolution of US Trade Sanctions. Longstanding sanctions would generally indicate a country-wide embargo, as is the case for Cuba and Iran. However, the Cuban and Iranian sanctions policies are currently in transition, as the traditional sanctions model is becoming deemphasized and would now only be used in extreme circumstances such as the case with North Korea. Sanctions imposed on African countries in 2005-2006 as highlighted in the diagram below were targeted sanctions based on human rights violations, concerns of regional stability or entities involved in undermining the democratic process.
Jurisdictional Risk and AML Systems
The evolution of sanctions highlights how US regulators perceive risk. In the case of the African countries outlined above, sanctions were imposed to prevent the flow of money to the groups and individuals participating in local conflicts. The sanctions imposed were designed to prevent or at least slow down human rights violations. The question is, could this same perception of situational and jurisdictional risk be applied to anti-money laundering (AML) systems?
The Traditional AML Model
Cross-border transfers could be monitored based on a number of factors, but generally models are comprised of three main elements:
- Frequency: The number of transfers which occurred within a specific time period. Example: 3 transfers over a rolling 7 day time period.
- Amount: The value of each transfer. Example: A minimum threshold of X dollars could be configured in the monitoring system. Other elements would include round dollar amounts and amounts just below minimum reporting requirements.
- Jurisdictional risk: The risk level or score associated with each country. Example: Transfers flowing through high-risk jurisdictions would generally receive greater scrutiny than similar transactions which only flowed through low-risk jurisdictions based on the financial institution’s country risk ranking.
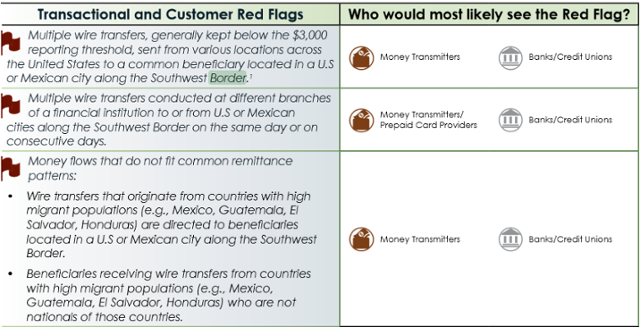
Financial Crimes Enforcement Network (FinCEN) Regulatory Guidance
On September 11, 2014 Financial Crimes Enforcement Network (FinCEN) released an advisory guide called “Guidance on Recognizing Activity that May be Associated with Human Smuggling and Human Trafficking – Financial Red Flags” which was intended to help financial institutions identify human trafficking red flags. The interesting part is that FinCEN specifically identified both US and Mexican cities on the Southwest border as areas which require additional scrutiny as described in the transactional and customer red flags listed below:
Source: https://www.fincen.gov/statutes_regs/guidance/pdf/FIN-2014-A008.pdf
Micro-Jurisdictions: The Southwest Border
The image of the Southwest border below illustrates that there are multiple cities in the United States and Mexico that would fall within FinCEN’s advisory.
Micro-Jurisdictions: The Tri-Border Area (TBA)
The Tri-Border area is the region where the borders of Brazil, Argentina, and Paraguay meet, which has been known as a criminal haven for organized crime groups, terror groups and drug traffickers. In a report titled “TERRORIST AND ORGANIZED CRIME GROUPS IN THE TRI-BORDER AREA (TBA) OF SOUTH AMERICA” the author describes various conditions in the Tri-Border Area (TBA) that are very favorable to organized crime and terror groups in the below quote:
The three cities which are highlighted in the report are Ciudad de Este, Foz do Iguaçu and Puerto Iguazú because of their proximity to all three countries’ borders.
Challenges of natural language processing (NLP)
Traditional AML systems usually have functionality to support a list of country codes which can be segmented into categories such as low, medium, high, and very high risk. As a result, transactions which flow through higher risk jurisdictions should, in theory, receive greater scrutiny than lower risk transactions. Financial institutions usually store country codes in various systems based on the International Organization for Standardization (ISO) standard (ISO 3166-1) which can be represented in three formats:
- ISO 3166-1 alpha-2: Two-letter country codes.
- ISO 3166-1 alpha-3: Three-letter country codes.
- ISO 3166-1 numeric: Three-digit country codes.
The guidance issued by FinCEN adds another layer of complexity to AML systems because the red flags are not contained in a predefined list of country codes, but in a free text field such as a city, which creates a number of challenges.
The image below shows an address in Ciudad Juarez. Mexico and many financial institutions will have similar field definitions to capture addresses in various systems for client on-boarding or to facilitate a transaction. The only field which is based on a predefined list is the country code and sometimes the state/province, but most of the other fields are free text. However, some financial institutions will attempt to validate the address based on the information given, but not all organizations have the capacity to do so.
If most traditional AML models rely on country codes as a key attribute to determine suspicious activity, then how will a free text city be handled?
The Micro-Jurisdiction AML Model
Essentially, the FinCEN advisory is pointing to an extension of the traditional AML model where one of the additional attributes in the model would be a micro-jurisdiction. The main three components (Frequency, Amount and Jurisdictional risk) of the traditional AML model would still apply, but a fourth attribute would need to be added to the model and calibrated accordingly.
- Frequency: The number of transfers which occurred within a specific time period. Example: 3 transfers over a rolling 7 day time period.
- Amount: The value of each transfer. Example: A minimum threshold of X dollars could be configured in the monitoring system. Other elements would include round dollar amounts and amounts just below minimum reporting requirements.
- Jurisdictional risk: The risk level or score associated with each country. Example: Transfers flowing through high-risk jurisdictions would generally receive greater scrutiny than similar transactions which only flowed through low-risk jurisdictions based on the financial institution’s country risk ranking.
- Micro-Jurisdictional risk: The risk level or score associated with specific towns, zip codes or cities. Example: Transfers flowing through high-risk micro-jurisdictions would generally receive greater scrutiny than a similar transaction which only flowed through low-risk micro-jurisdictions based on the financial institution’s risk ranking.
The Implications of Micro-Jurisdictional Risk
If regulators continue to issue guidance which highlights specific geographic areas as part of a money laundering typology, then traditional AML systems must evolve or engage third party vendors which can process large volumes of data quickly, and without impacting the daily operations of the financial institution’s overall AML program. Another question which comes to mind is to what extent financial institutions should be proactive?
Should financial institutions begin to gather their own intelligence to identify potential high-risk micro-jurisdictions or should they wait for advisories from their respective regulators? The amount of intelligence gathered could be relative to the financial institution’s risk appetite and geographic footprint.
Traditional AML systems may not be the optimal solution to process large volumes of data to extract towns, zip codes and cities from free text fields. Hence, using a third party solution based on the latest advances in computing technology that can cleanse, prepare and risk rate the data before it is sent to the traditional AML systems would be beneficial to financial institutions.
Identifying and monitoring high-risk micro-jurisdictions could extend a financial institution’s AML program’s sophistication by focusing on the more granular attributes of transactional activity and consequently pushing the risk-based approach to new horizons.
Cyber Fraud on the Rise in Southeast Asia
A series of cyber fraud attacks targeting financial institutions through the SWIFT global messaging system has prompted an industry wide review of IT security measures and has highlighted the rising risk of cyber fraud against financial institutions in Southeast Asia and beyond. SWIFT has responded with a five-part customer security program to reinforce the security of the global banking platform, yet its CEO has warned “there will be more attacks.”
Editor's Note: This article originally appeared on the Corporate Compliance Insights on June 23, 2016.
A series of cyber fraud attacks targeting financial institutions through the SWIFT global messaging system has prompted an industry wide review of IT security measures and has highlighted the rising risk of cyber fraud against financial institutions in Southeast Asia and beyond. SWIFT has responded with a five-part customer security program to reinforce the security of the global banking platform, yet its CEO has warned “there will be more attacks.”
Cyber fraud risk is heightened in developing countries that often lack the technological resources to detect and thwart such attacks, while geopolitical dynamics also play into the risk equation. In light of these factors, Access Asia views Southeast Asia as a region of heightened risk for cyber fraud targeting financial institutions due to socioeconomic conditions, proximity to suspected centers of cyber fraud operations in North Korea and China and the existence of strong transnational criminal networks.
Indeed, one of the most recent cases to come to light involves an attempted attack on Vietnam’s Tien Phong Bank (TP Bank), while the money trail of an $81 million cyber heist from the State Bank of Bangladesh’s account at the New York Federal Reserve in February has been traced to the Philippines. Hong Kong (which lies on the periphery of Southeast Asia) is the reported end of the money trail for a US$2 million cyber theft on an Ecuadorian bank in early 2015, while the Philippines was also the target of an earlier attack in October 2015.
Access Asia views Cambodia, Myanmar, Indonesia and the Philippines as the countries most at risk in Southeast Asia for future cyber fraud attacks targeting financial institutions due to a perception of lax IT security measures, weak governance and law enforcement, high levels of corruption that could facilitate inside collusion and the existence of well-established transnational criminal networks.
North Korean involvement?
Many cybersecurity experts believe these SWIFT attacks have been conducted by the same group of hackers due to the similarities of the malware used and link the same group with the 2014 hacking attack on Sony Pictures Entertainment. The FBI concluded the 2014 attack was perpetrated by North Korea, which makes the rogue nation a key suspect in these SWIFT attacks. However, many security experts outside the IT realm refute direct North Korean involvement in these SWIFT attacks, questioning why a nation-state would engage in cyber theft, particularly given the relatively small amount of money involved in them (with the exception of the attack on Bangladesh Bank.) Moreover, these attacks would have required a number of agents operating in numerous countries to coordinate both the attacks and retrieval of the money, likely with the cooperation of other international criminal networks – a modus operandi not fitting with North Korea in Southeast Asia. The North Koreans tend to be tightly nationalistic and unwilling to trust other ethnic groups – especially criminals – and are most unlikely to be dealing with international crime groups in Southeast Asia.
“DPRK is usually vilified given their ‘last rogue nation standing’ status; however, there are some underlying changes at work that most outside do not realize due to the media’s lack of positive coverage,” noted one of Access Asia’s China-based security partners who recently co-authored a report on the internal political dynamics of North Korea. “I’m hearing that it’s more likely Russian or Chinese hackers,” the source added.
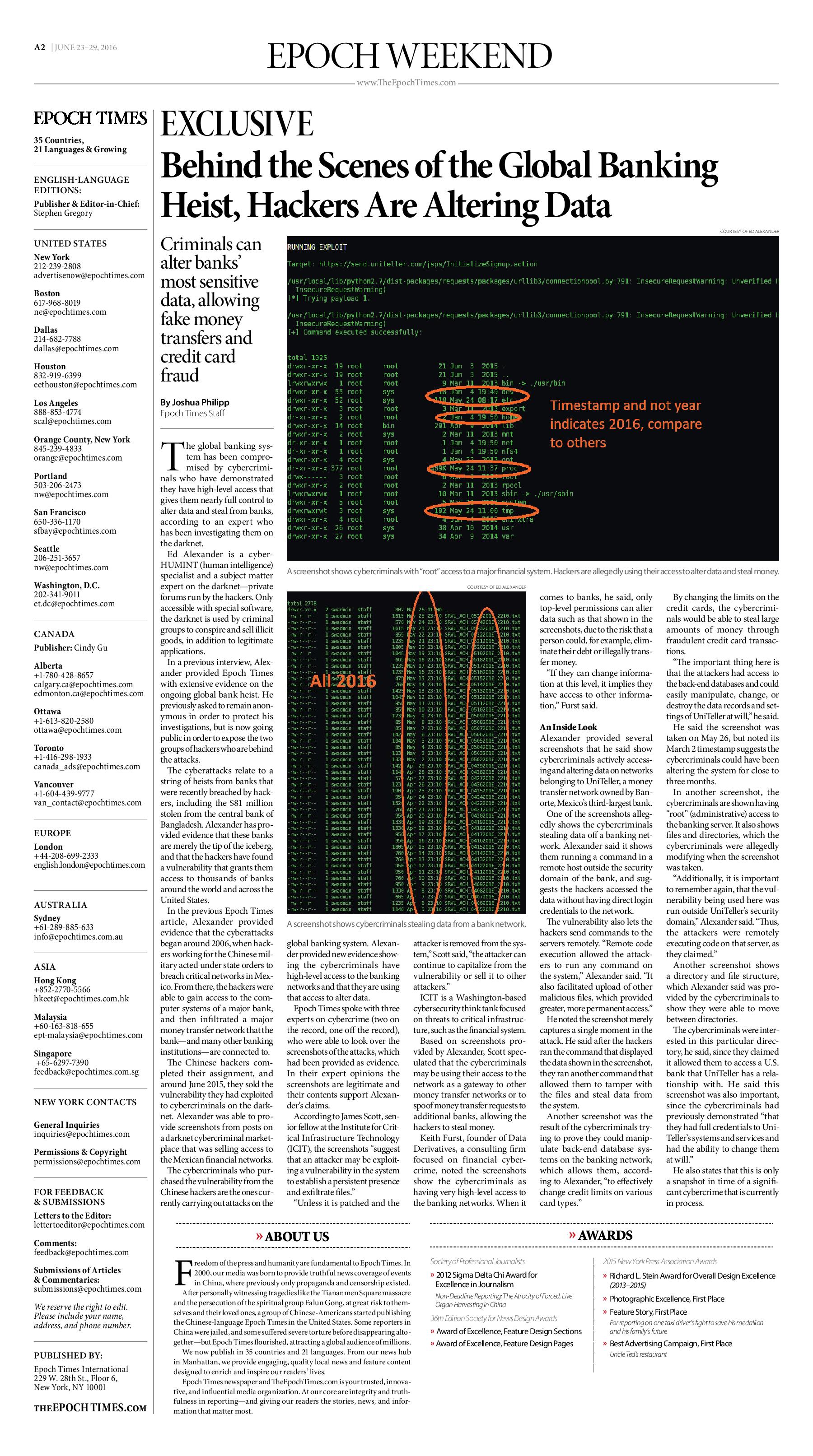
A recent investigative report in the Epoch Times, which cited an insider with reportedly direct knowledge of the recent attacks, puts the blame on former Chinese state hackers who identified the initial vulnerability and then sold the information to cyber crime groups.
No matter who is responsible for these recent attacks, greater emphasis should be placed on enhancing security defenses to protect against future attacks. In Vietnam, the country’s leading network security firm BKAV believes 30 percent of Vietnamese commercial banks’ websites have vulnerabilities, two-thirds of which are at medium or high risk for cyber attacks. This figure is likely much higher in lesser developed Southeast Asian countries, such as Cambodia and Myanmar.
New fraud detection models needed
“The recent SWIFT attacks definitely point to the need for tighter cybersecurity protocols, but even such tighter measures may not be enough,” explained Keith Furst, founder and a financial crimes technology consultant at Data Derivatives. “There are other ways to initiate payments through social engineering or even by holding a key employee’s family hostage in an extreme example – so when the security measures fail, what else can be done?”
Furst suggests developing a model in which banks could detect fraudulent activity to the SWIFT payment traffic before the messages leave the bank’s network. Using the example of detecting credit card fraud through historical profiling and blocking transactions that are deemed to be a deviation from that profile, Furst believes similar fraud detection models could potentially be applied to SWIFT traffic before the messages leave the bank’s network. Furst explained:
“Think of it kind of like an expected range of values where the currency, amount, banks and countries involved in the payment activity all contribute to the historical profile. So, in the case of Bangladesh Bank, if they had these type of models running for all SWIFT messages, then they may have detected that something was off when $951 million worth of instructions were requested. The final beneficiaries of the transfers could also be a strong indication of fraud, because why would the Bangladesh Bank send such high-value transfers to beneficiaries they don’t normally deal with on a regular basis? In essence, it is taking what financial institutions have learned from anomaly detection and fraud models and applying it to SWIFT traffic before the transfers leave the bank’s network.”
As heightened security measures are being debated and developed, financial institutions should remain vigilant and aware that the group or groups responsible for these recent bank attacks will likely strike again. Security software company Symantec warns that these attacks are part of a “wide campaign against financial targets in the region” and that recent publicity of the attacks “may prompt other attack groups to launch similar attacks.”
“The recent SWIFT attacks may be only the beginning of a larger scale campaign where cyber criminal organizations systemically target weak banks and exploit known vulnerabilities,” said Data Derivative’s Furst. “Recent events may accelerate discussions surrounding groundbreaking technological innovations, such as using a blockchain ecosystem as an alternative for high-value, cross-border money transfer,” he added.
Meanwhile, SWIFT officials are warning all banks to review their security controls and to take special care with PDFs.
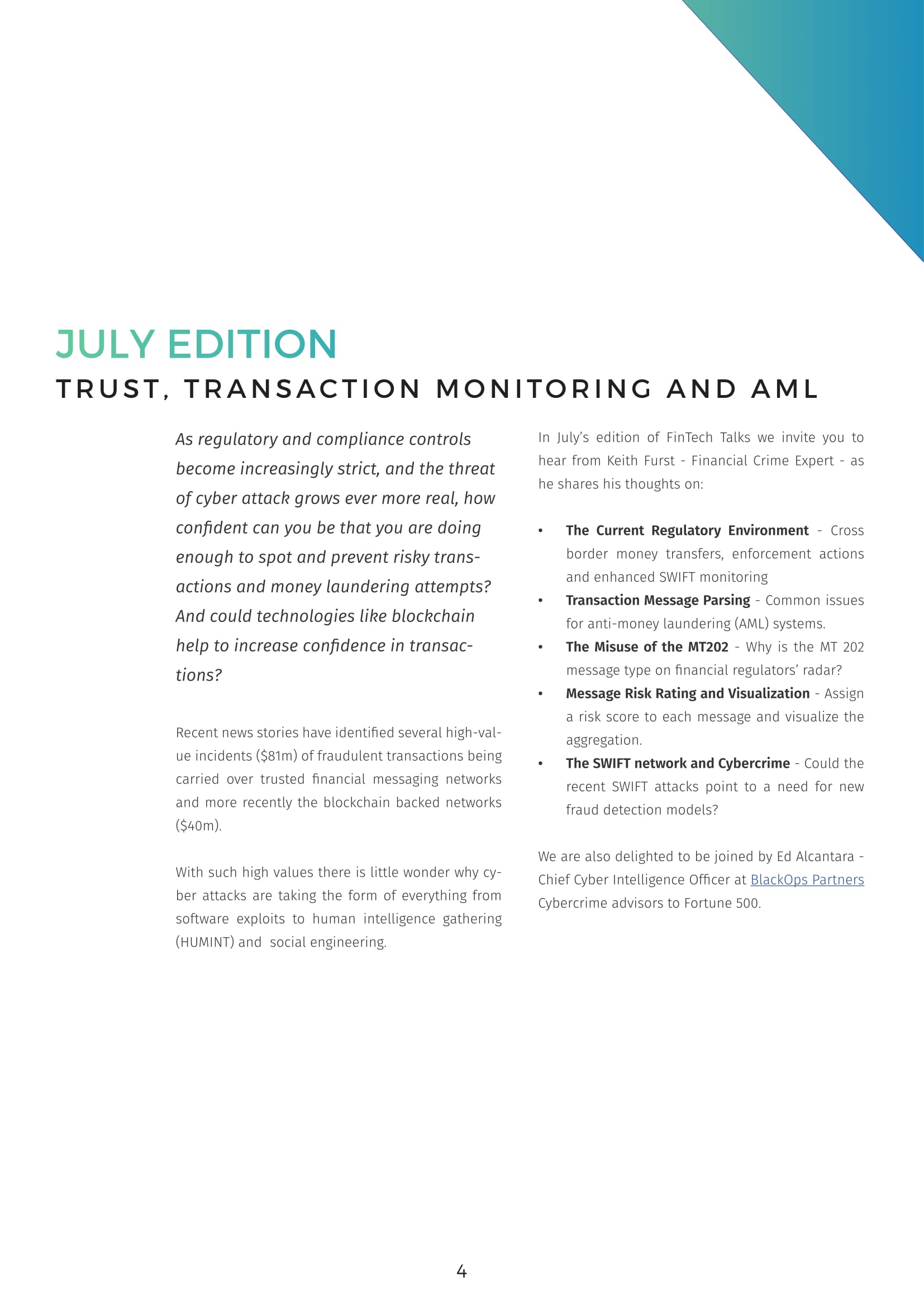
TRUST, TRANSACTION MONITORING AND AML FOR SWIFT MESSAGING
As regulatory and compliance controls become increasingly strict, how confident can you be that you are doing enough to spot and prevent risky SWIFT transactions and money laundering attempts?
As regulatory and compliance controls become increasingly strict, how confident can you be that you are doing enough to spot and prevent risky SWIFT transactions and money laundering attempts?
Join us on July 14th as we discuss Trust, Transaction Monitoring, and AML for SWIFT messaging.
EXCLUSIVE: Hackers Compromise Global Banking System at Highest Level, Investigator Reveals
The global banking system has been compromised by cybercriminals who have demonstrated they have high-level access that gives them nearly full control to alter data and steal from banks, according to an expert who has been investigating them on the darknet.
Editor's Note: This article originally appeared in The Epoch Times on June 23, 2016.
Five (5) Crucial Steps Financial Institutions Can Follow to Prepare for a Backlog of Customer Due Diligence Reviews
It’s a dynamic time in the financial crimes world and this is especially true for Customer Due Diligence (CDD) regulations, as demonstrated by the following recent developments:
- The leak of the Panama Papers highlighted well-known fears in the financial compliance world that the use of shell companies obfuscates the true ownership of the entities.
- Financial Institutions (FI) are working to comply with the new rules on beneficial ownership.
- The Financial Crimes Enforcement Network (FinCEN) released the “Customer Due Diligence Requirements for Financial Institutions; Final Rule” on May 11, 2016.
Editor's Note: This article originally appeared on the Prescient blog on June 15, 2016.
It’s a dynamic time in the financial crimes world and this is especially true for Customer Due Diligence (CDD) regulations, as demonstrated by the following recent developments:
- The leak of the Panama Papers highlighted well-known fears in the financial compliance world that the use of shell companies obfuscates the true ownership of the entities.
- Financial Institutions (FI) are working to comply with the new rules on beneficial ownership.
- The Financial Crimes Enforcement Network (FinCEN) released the “Customer Due Diligence Requirements for Financial Institutions; Final Rule” on May 11, 2016.
In adapting to these new realities, many financial institutions have been reevaluating their KYC programs and enhancing their current policies, procedures and systems. The recent FinCEN release will only expedite this process as financial institutions invest in new KYC technologies to keep up with the shifting regulatory climate.
KYC Projects Required to Comply with New Rules
FinCEN describes in the “Customer Due Diligence Requirements for Financial Institutions; Final Rule” document that the new requirements for beneficial ownership are similar to the existing Customer Identification Programs (CIP) already in place at financial institutions. Since beneficial ownership requires the financial institution to ask questions that it may not currently be asking of its customers, certain technology projects need to be initiated to enhance current on-boarding systems or possibly implement new platforms. CDD projects can be some of the most complex financial crimes projects to execute with a high degree of accuracy, due to the number of people involved and the potential to adversely impact client-facing processes. This stands in stark contrast to the implementation of transaction monitoring systems (TMS), which has essentially no impact on the customer experience and therefore is given less urgency by senior management to get it right the first time.
Given the criticality of these projects to regulatory and compliance success, financial institutions must implement the following five key steps to mitigate risks associated with a customer due diligence backlog.
Step 1: Defining the Requirements
Financial Institutions must define the requirements of their new Customer Due Diligence (CDD) models to meet current regulatory guidelines, such as for beneficial ownership. Given the new requirements for capturing beneficial owner information, it is prudent for financial institutions to review their current customer risk rating methodology. Key items to be evaluated include:
- What is the definition of a customer?
- How can the amalgam of customer information – scattered across multiple disparate systems – be synthesized to arrive at a holistic view of the customer?
- Under what conditions is Enhanced Due Diligence (EDD) on a customer required?
- Is it simply based on the customer type, such as a Money Service Bureau (MSB), a precious metal dealer, a casino, a high cash intensive business, among others?
- Or could the risk model score a seemingly low-risk customer as high-risk based on the numerous accounts held across various business lines? In instances where false-positive hits are possible, financial institutions should weigh the benefits of escalating the depth of due diligence to fully elucidate all risk factors.
Once this initial review is completed, a new customer risk rating methodology should be built to meet the financial institution’s specific requirements.
Step 2: Deciding on In-House Development or Vendor Selection
Institutions must decide whether to utilize a Customer Due Diligence (CDD) vendor or develop the software in-house. In ideal projects, this will be an extension of the requirements step, as the particular data requirements need to be documented. Models are mere approximations that attempt to provide an accurate depiction of reality, but there are always assumptions and limitations with every quantitative model that need to be acknowledged, especially by financial institutions implementing or enhancing KYC systems. To address these concerns, financial institutions will need to make decisions on whether they will purchase software from a CDD vendor or develop the model in-house. For particularly complex CDD projects, an Enhanced Due Diligence vendor should also be identified to escalate the level of scrutiny.
Step 3: Implementation
Required changes will be made to new or existing client on-boarding applications to gather additional information on the customer for risk scoring. This step is subject to deficiencies such as requirement gaps, configuration errors, data quality issues and lack of data for model optimization. Changes will need to be made to multiple systems, and new technologies may need to be implemented to support the new custom risk rating methodology. First, the on-boarding applications need to be enhanced to ask the customer additional questions (including those regarding beneficial ownership information), or to collect additional personally identifiable information. Second, the CDD system needs to be enhanced or possibly implemented from scratch to consume these new data elements and consider them for risk scoring. Finally, the CDD system needs to have specific rules that will add a point score for each attribute that the risk model is considering, such as country of incorporation, politically exposed person (PEP) status and products being used, among others. Optimizing the transactional system is a much easier task—in principle—than optimizing the KYC systems, because there is usually a significant amount of historical activity to reference. However, new customer information is generally captured in incremental waves, and using samples to forecast how many customers will fall into each risk category can be troublesome. The lack of data to optimize the system is a risk “in and of itself.”
Step 4: System Delivery
A new Customer Due Diligence (CDD) model is delivered and the additional customer information captured by the on-boarding systems is passed to the risk scoring engine. Alerts on high-risk customers and periodic reviews are traditionally generated in an incremental fashion. Once the new KYC system is fully operational, customers are asked additional questions based on the new customer risk rating model. Alternatively, a customer may inquire about a new product and trigger the KYC process to commence, where they would be prompted to answer additional questions as defined by the model. Essentially, what is happening is that the risk scoring application receives a slow-but-steady flow of new customers to evaluate. Be aware, though, that unless the financial institution’s new risk rating methodology focuses mainly on historical attributes – which is usually not the case – then it could be difficult for the enterprise to determine how many high-risk customers it actually serves.
Step 5: Backlog of Reviews
The Customer Due Diligence (CDD) model can potentially generate more alerts than expected, and this could lead to a precarious situation for financial institutions. Implementing new models is risky, although neglecting to implement new models could be even riskier. Financial institutions must be aware of implementation factors that could cause a CDD system to produce unwarranted spikes in alerts: improper execution of the implementation; use of model risk scoring that is too conservative; or unexpected behavior from customers. Some questions that a financial institution should consider throughout the implementation of a new CDD system include:
- If more high-risk customer alerts are generated than expected, how will this situation be handled?
- Will additional CDD investigators be hired on a full-time or contract basis?
- Will the level of due diligence be escalated by engaging an Enhanced Due Diligence (EDD) vendor?
- Does the customer risk scoring model need to be reviewed in terms of its accuracy with regard to the financial institution’s risk appetite?
- If tactical changes are truly required for the customer risk rating methodology, how long will it take to complete the analysis, document proposed changes and implement those changes to reduce the number of high-risk customer alerts?
- If the CDD system requires recalibration due to a spike in high-risk customer alerts, will the institution have a way to scale up and produce high-quality CDD reviews in a matter of days?
Finding the Right Balance
At the end of the day, financial institutions – in the face of new regulatory challenges – must decide for themselves which competing factors to prioritize in planning for a Customer Due Diligence backlog. In taking stock of risk scoring models, options for vendor selection and efficient methods for implementation, a well-thought-out CDD program can instill confidence and peace of mind in the success of a financial compliance program.
Recent attacks highlight the rising risk of cyber fraud for SE Asian banks
A series of cyber fraud attacks targeting financial institutions through the SWIFT global messaging system has prompted an industry-wide review of IT security measures and has highlighted the rising risk of cyber fraud against financial institutions in Southeast Asia and beyond. SWIFT has responded with a five-part Customer Security Programme to reinforce the security of the global banking platform, yet its CEO has warned “there will be more attacks.”
Editor's Note: This article originally appeared on the Access Asia Consulting blog on June 6, 2016.
A series of cyber fraud attacks targeting financial institutions through the SWIFT global messaging system has prompted an industry-wide review of IT security measures and has highlighted the rising risk of cyber fraud against financial institutions in Southeast Asia and beyond. SWIFT has responded with a five-part Customer Security Programme to reinforce the security of the global banking platform, yet its CEO has warned “there will be more attacks.”
Cyber fraud risk is heightened in developing countries that often lack the technological resources to detect and thwart such attacks. In addition, geo-political dynamics and the presence of sophisticated transnational criminal networks also play into the risk equation, all making certain areas of the world more vulnerable than others. In light of these factors, Access Asia views Southeast Asia as a region of heightened risk for cyber fraud targeting financial institutions due to socio-economic conditions, proximity to suspected centers of cyber fraud operations in North Korea and China, and the existence of strong transnational criminal networks.
Indeed, the most recent case to come to light involves an attempted attack on Vietnam’s Tien Phong Bank (‘TP Bank’), while the money trail of an $81-million cyber heist from the State Bank of Bangladesh’s account at the New York Federal Reserve in February has been traced to the Philippines. Hong Kong (which lies on the periphery of Southeast Asia) is the reported end of the money trail for a US$2 million cyber theft on an Ecuadorian bank in early 2015, while the Philippines was also the target of an earlier attack in October 2015.
North Korean involvement?
Many cyber security experts believe these SWIFT attacks have been conducted by the same group of hackers due to the similarities of the malware used and link the same group with the 2014 hacking attack on Sony Pictures Entertainment. The FBI concluded the 2014 attack was perpetrated by North Korea, which makes the rogue nation a key suspect in these SWIFT attacks. However, many security experts outside the IT realm refute direct North Korean involvement in these SWIFT attacks, questioning why a nation-state would engage in cyber theft, particularly given the relatively small amount of money involved in them (with the exception of the attack on Bangladesh Bank.) “DPRK is usually vilified given their ‘last rogue nation standing’ status, however there are some underlying changes at work that most outside do not realize due to the media’s lack of positive coverage,” noted one of Access Asia’s China-based security partners who recently co-authored a report on the internal political dynamics of North Korea. “I’m hearing that it’s more likely Russian or Chinese hackers,” the source added.
Still, Access Asia believes the possibility of North Korean involvement should not be ruled out, yet greater emphasis should be placed on enhancing security defenses to protect against future attacks.
New fraud detection models needed:
“The recent SWIFT attacks definitely point to the need for tighter cyber-security protocols, but even such tighter measures may not be enough,” explained Keith Furst, founder and financial crimes technology consultant at Data Derivatives. “There are other ways to initiate payments through social engineering or even by holding a key employee’s family hostage in an extreme example – so when the security measures fail what else can be done?”
Furst suggests developing a model in which banks could detect fraudulent activity to the SWIFT payment traffic before the messages leave the bank’s network. Using the example of detecting credit card fraud through historical profiling and blocking transactions that are deemed to be a deviation from that profile, Furst believes similar fraud detection models could potentially be applied to SWIFT traffic before the messages leave the bank’s network. Furst explained:
“Think of it kind of like an expected range of values where the currency, amount, banks and countries involved in the payment activity all contribute to the historical profile. So, in the case of Bangladesh Bank, if they had these type of models running for all SWIFT messages then they may have detected that something was off when $951 million worth of instructions were requested. The final beneficiaries of the transfers could also be a strong indication of fraud because why would the Bangladesh Bank send such high value transfers to beneficiaries they don’t normally deal with on a regular basis? In essence, it is taking what financial institutions have learned from anomaly detection and fraud models and applying it to SWIFT traffic before the transfers leave the bank’s network.”
As heightened security measures are being debated and developed, financial institutions should remain vigilant and aware that the group or groups responsible for these recent bank attacks will likely strike again. Security software company Symantec warns that these attacks are part of a “wide campaign against financial targets in the region” and that recent publicity of the attacks “may prompt other attack groups to launch similar attacks.”
Access Asia views Cambodia, Myanmar, Indonesia and the Philippines as the countries most at risk in Southeast Asia for future cyber fraud attacks targeting financial institutions due to a perception of lax IT security measures, weak governance and law enforcement, high-levels of corruption that could facilitate inside collusion, and the existence of well-established transnational criminal networks.
SWIFT officials are warning all banks to review their security controls and to take special care with PDFs.
Money Laundering Conference in Canada 2016
Happy to announce I will be presenting at the 14th installment of Canada’s premier event in the field of money laundering compliance and control. The theme of Money Laundering in Canada 2016 is Financial Crime, Compliance, and Regulation: Keeping Pace with the Times.
Look forward to seeing some of you on October 2 -4, 2016 at the Toronto Marriott Downtown Eaton Centre in Toronto, Ontario, Canada.
How the misuse of SWIFT MT 202 is fuelling financial crime
The September 11, 2001 terrorist attacks on the United States could be one of the most redefining moments of the 21st century as the chain of events which followed still has a significant impact on our daily lives today. Airplane hijackings are not a new phenomenon as the first one recorded occurred on February 21, 1931 in Arequipa, Peru. Since 1931 there have been dozens of hijackings across the globe, therefore some would argue that there was a tremendous security gap in the airline industry which could have been addressed prior to 9/11. Implementing the type of airport security we have today may have been perceived as cost prohibitive prior to 9/11, yet who would have ever thought that someone would be capable of using a passenger plane as a missile? While crashing planes as a means of destruction is not a new concept, as this was done by the Japanese Kamikaze in World War II, it seems that our moral integrity could not conceive of using a passenger plane with innocent civilians on it to attack another civilian site.
Editor's Note: This article originally appeared on the Gresham Tech blog on April 5, 2016.
The September 11, 2001 terrorist attacks on the United States could be one of the most redefining moments of the 21st century as the chain of events which followed still has a significant impact on our daily lives today. Airplane hijackings are not a new phenomenon as the first one recorded occurred on February 21, 1931 in Arequipa, Peru. Since 1931 there have been dozens of hijackings across the globe, therefore some would argue that there was a tremendous security gap in the airline industry which could have been addressed prior to 9/11. Implementing the type of airport security we have today may have been perceived as cost prohibitive prior to 9/11, yet who would have ever thought that someone would be capable of using a passenger plane as a missile? While crashing planes as a means of destruction is not a new concept, as this was done by the Japanese Kamikaze in World War II, it seems that our moral integrity could not conceive of using a passenger plane with innocent civilians on it to attack another civilian site.
MT 202 background
The banking industry reacted to the 9/11 terrorist attacks in many ways, but one was addressing the transparency concerns of *MT 202 message type as described by the Basel Committee on Banking Supervision in the paper “Due diligence and transparency regarding cover payment messages related to cross-border wire transfers” which was published in May of 2009.
Cross-border wire transfers usually involve several different financial institutions located in different jurisdictions. The SWIFT MT 202 was used to facilitate both customer credit and interbank transfers historically. In an effort to decrease processing time an originating bank could send a MT 202 message to an intermediary bank and send the MT 103 (customer credit transfer) directly to the beneficiary bank. However, this practice would conceal the true originator and beneficiary of the message from the intermediary bank because the MT 202 does not have the originator and beneficiary fields. The risk to the intermediary bank included, but was not limited to the following:
- Sanctions screening on the originator and beneficiary would not be performed.
- The originating bank could be in a jurisdiction with different sanction watch lists and the technical capabilities of each bank’s sanction screening program could vary.
- Suspicious activity monitoring on the underlying originator and beneficiary in the message would not be performed.
- Originating banks could be intentionally using the “cover” method (MT 202 and MT 103) to obfuscate the true originator and beneficiary of the transfer from the intermediary financial institutions.
To address these transparency concerns the Society for Worldwide Interbank Financial Telecommunications (SWIFT) created a new MT 202 COV message type, which contained mandatory fields for both the originator and beneficiary of a payment, on November 21, 2009.
When to use the MT 202 COV?
As per the guidance issued in the “2009 Standards Release” the use the MT 202 COV is defined as follows:
“This message is sent by or on behalf of the ordering institution directly, or through correspondent(s), to the financial institution of the beneficiary institution. It must only be used to order the movement of funds related to an underlying customer credit transfer that was sent with the cover method. The MT 202 COV must not be used for any other interbank transfer. For these transfers the MT 202 must be used.”
What is a “cover payment”?
Again, a cover payment can be defined as a transfer with two separate message streams such as the MT 103 and MT 202.
- The MT 103 is a direct payment order to the beneficiary’s bank.
- The MT 202 is an interbank order to an intermediary bank or banks to cover the originator bank’s obligation to reimburse the beneficiary bank.
Cover Payment example
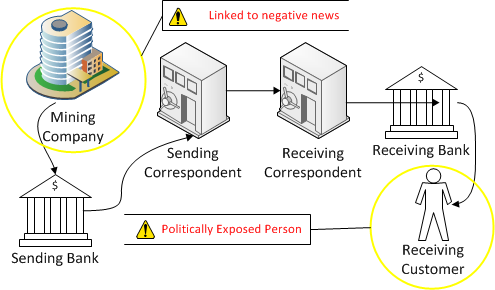
Before the implementation of the MT 202 COV message type the following cover payment would be common practice. Furthermore, using this method for customer credit transfers conceals the underlying originator and beneficiary from the intermediary banks.
In the diagram above, the originating customer is located in Japan and wants to pay the beneficiary customer located in Bosnia and Herzegovina in local currency, which is the Bosnian Convertible Marka (BAM). The originating bank is not able to send the payment order directly to the beneficiary bank so it must use one of its correspondent banks. The high level message flow is as follows:
- Originating customer in Japan instructs originating bank to pay beneficiary customer in Bosnian Convertible Marka (BAM).
- Originating bank sends MT 103 directly to beneficiary bank to pay beneficiary customer in Bosnian Convertible Marka (BAM).
- Beneficiary bank sends MT 199 to originating bank requesting reimbursement in United States Dollars (USD).
- Originating bank sends MT 202 to one of its sending correspondent banks to pay the beneficiary bank in United States Dollars (USD).
- The MT 202 does not disclose the originator and beneficiary customer of the transfer because the fields are not available in the MT 202 message type.
- The sending correspondent bank sends the MT 202 to the receiving correspondent bank.
- The receiving correspondent bank sends the MT 202 to the beneficiary bank and finally covers the MT 103 which was sent directly from the originating bank to the beneficiary bank.
US Regulators sensitive to cover payments
In the Statement of Facts released by the US Department of Justice in the case against BNP Paribas, S.A. (BNPP) it stated the following about “cover payments”:
“In March and June 2006, BNPP received two additional legal opinions from U.S. Law Firm 1, which informed BNPP that (a) U.S. sanctions could apply to BNPP even when the transactions were processed by U.S. Bank 1 instead of BNPP New York, and (b) U.S. authorities had become especially sensitive to the use of “cover payments” by foreign banks that omitted underlying descriptive details about the nature of the transactions, and advised BNPP to “ensure that they had adequate procedures in place to guard against any abuses of cover payment messages that could cause their U.S. operations to engage in prohibited transactions under U.S. sanctions.”
Detecting the misuse of the MT 202 message type?
How could an intermediary bank detect if the MT 202 message type has been misused if regulators are becoming sensitive to the use of “cover payments”? One method an intermediary bank can implement is to check the MT 202 message details for keywords such as “cover”, “MT 103”, “further credit to”, etc. However, searching for these keywords in the MT 202 message details will only provide an indication that the cover payment method was used, but it doesn’t determine if the message type has been misused. To determine if the MT 202 has been misused the correspondent bank will have to contact its customer which could be the originating or beneficiary bank and request a copy of the MT 103 message type. Once, the intermediary bank has a copy of the MT 103 its investigation unit can determine if the MT 202 message type has been misused or not.
Intermediary banks monitoring the potential misuse of the MT 202 message type is a labor intensive effort, but is there a way to decrease costs and increase efficiencies while remaining proactive and compliant?
What is the definition of an interbank transfer?
One of the reasons why monitoring the potential misuse of the MT 202 message type is extremely labor intensive stems from the amount of MT 202 message traffic which contains non-financial institution third parties appearing to be related to trade finance transactions, such as letter of credits. While each bank should have its own written policy and interpretation of the regulatory guidelines, there seems to be a consensus that non-financial institution third parties can be involved in a “cover payment” via the MT 202 and MT 103 message streams if the transaction is a letter of credit as this would be considered an interbank transfer.
Are the regulatory guidelines of an interbank transfer too ambiguous?
If regulators are sensitive to the potential misuse of “cover payments” then is the definition of an interbank transfer too broad? For example, if the guidance stated that all transfers which contain non-financial institution third parties should use the MT 202 COV and MT 103 message streams then it would make it easier for intermediary banks to detect the potential misuse of the MT 202 message type.
Final thoughts
On the condition that your bank is originating SWIFT traffic, then do written policies and procedures exist which clearly define when and when not to use the MT 202 message type?
Providing that your bank acts as an intermediary, then are there monitoring programs in place which can detect the potential misuse of the MT 202 message type? How would the potential misuse of the MT 202 message type be investigated? Furthermore, if the MT 202 has been misused by an originating bank then what would be the next steps to remedy the situation to ensure it doesn’t continue to recur?
Intermediary banks can leverage data visualization dashboards to monitor the potential misuse of the MT 202 message type because the traditional transaction monitoring systems (TMS) are too narrowly focused at the customer and account level and create a high number of false positives for the bank’s investigation unit.
*When the MT 202 message type is mentioned it should be understood to mean MT 202 and / or MT 205.
The challenges and benefits of mapping SWIFT messages to your Transaction Monitoring System (TMS)
The Regulatory landscape and SWIFT messages
Cross-border payments have been a central theme in recent regulatory actions where regulators levied record breaking fines against financial institutions that failed to comply with Bank Secrecy Act / anti-money laundering (BSA / AML) regulations. The Society for Worldwide Interbank Financial Telecommunications (SWIFT) is, in some sense, at the heart of these violations because it is one of the major facilitators of global money transfers which have come under increased scrutiny.
Editor's Note: This article originally appeared on the Gresham Tech blog on February 18, 2016.
The Regulatory landscape and SWIFT messages
Cross-border payments have been a central theme in recent regulatory actions where regulators levied record breaking fines against financial institutions that failed to comply with Bank Secrecy Act / anti-money laundering (BSA / AML) regulations. The Society for Worldwide Interbank Financial Telecommunications (SWIFT) is, in some sense, at the heart of these violations because it is one of the major facilitators of global money transfers which have come under increased scrutiny.
The enforcement actions came about for a range of reasons, but a general assertion made by regulators in many of the major violations was that banks had inadequate Bank Secrecy Act / anti-money laundering (BSA / AML) programs. A press release issued by the Department of Justice (DOJ) illustrates how regulators perceive failures of anti-money laundering (AML) programs to be a major infraction by financial institutions.
“A four-count felony criminal information was filed today in the District of Columbia charging Commerzbank with knowingly and willfully conspiring to commit violations of IEEPA and Commerz New York with three violations of the BSA for willfully failing to have an effective anti-money laundering (AML) program, willfully failing to conduct due diligence on its foreign correspondent accounts, and willfully failing to file suspicious activity reports. Assuming the bank’s continued compliance with the deferred prosecution agreement, the government has agreed to defer prosecution for a period of three years, after which time, the government would seek to dismiss the charges.”
What does an effective anti-money laundering (AML) program mean?
Effective anti-money laundering programs involve a wide variety of activities, resources, leadership and technology, but for the purpose of this article, the focus will be to discuss what improvements can be made when mapping SWIFT messages to transaction monitoring systems (TMS) and the common pitfalls and data quality issues which arise from this endeavor.
Transaction monitoring systems (TMS) are software applications which have been specifically designed to assist financial institutions to satisfy their BSA / AML requirements by leveraging pattern recognition algorithms that detect activity abnormalities and other money laundering typologies. Financial institutions involved in cross-border payments may be members of SWIFT, and consequently some of the institution’s SWIFT traffic may be subject to BSA / AML monitoring requirements based on their local jurisdiction's rules and regulations.
Mapping SWIFT messages to transaction monitoring systems (TMS)
Data mapping can be a difficult task in itself based on the wide variety of source system applications and middleware a financial institution can be supporting, but some transactional activity is more complex than others to map based on its structure and the number of data elements involved. This is particularly evident when a financial institution maps SWIFT messages to its transaction monitoring system (TMS). Some of the challenges stem from, but are not limited to the following:
- Number of entities involved in the message
- Financial institutions, large corporations, businesses and individuals
- Different SWIFT message types and formats to facilitate various banking functions such as trade finance, foreign exchange, securities settlements, cross border payments, etc.
- Periodic updates and changes to SWIFT message formats and validations
- Free text format of certain fields
- Options to represent the same data differently in the same field
- Large reference data sets required to extract the necessary data for Compliance
- Development of in-house message parsing tools subject to limitations and inaccuracies
- Inflexible vendor solutions that can parse messages, but not to the extent needed for transaction monitoring systems (TMS)
- Knowledge gap between personnel in payment operations and the individuals implementing the transaction monitoring systems (TMS)
Levels of complexity
Financial institutions can vary quite significantly in terms of how sophisticated their monitoring of SWIFT messages is, but all are subject to a certain level of inaccuracy. The table below illustrates three levels of complexity for the mapping of SWIFT messages to a transaction monitoring system (TMS).
Correspondent banks and other financial institutions
Financial institutions which support correspondent banking will be inclined to implement the intermediate and advanced levels of SWIFT message mapping, especially in the more developed countries, because of the amount of scrutiny placed on banks from regulators for engaging in this business. Correspondent banking is considered very risky because the correspondent bank providing clearing services to their respondent banks are predominantly relying on their respondents to have an adequate BSA / AML program. However, respondent banks generally will abide by the rules and regulations of their host country which could differ from the correspondent’s and the perception and risk appetite of each institution can also vary widely.
Financial institutions which do not provide correspondent banking services can still benefit significantly from implementing the intermediate and advanced level of SWIFT data mapping because of the increased detection capabilities the data offers.
Common inaccuracies
If a SWIFT message is not parsed correctly it could misrepresent which role each financial institution played in the message such as the originating bank, sending correspondent, receiving correspondent, beneficiary bank or other type of intermediary.
1. Bank roles and countries in the message flipped
The diagram below represents a MT103 SWIFT message where there are four banks and two customers involved in the message. However, the originating and sending correspondent bank roles have been flipped and the actual sending correspondent bank is represented as the originating bank, and the originating bank appears as the correspondent.
2. Wrong bank and country represented in the message
In the second example in the diagram below, the financial institutions are not flipped, but the originating bank is actually represented incorrectly. The originating bank appears to be located in Mexico, but the bank is actually located in France.
3. Key risk attributes missed in basic mapping model
Another more insidious example that represents the limitations and lack of transparency of mapping SWIFT messages according to the basic level of complexity is shown in the diagram below. First, the originating bank and its country code is unable to be identified because the basic parsing model expects a SWIFT (BIC) to be supplied, but the originating bank’s name and address was populated instead. Second, the basic parsing model is not sophisticated enough to extract the country codes from the originating and beneficiary customer address fields and consequently this key information is blank.
If the mapping model was able to extract the country code from the originating and beneficiary customer address fields, then the Compliance department would have the opportunity to create a new detection scenario such as the customer banking outside of their jurisdiction. While there are instances where an entity can have a legitimate reason to bank outside of its jurisdiction it is an important risk indicator that can be leveraged and help the institution fine tune its system by implementing a more targeted and risk based approach.
Why does accuracy matter?
While on an individual transaction level the inaccuracies described above may appear to be trivial, on a macro scale it could severely undermine a financial institution’s ability to monitor abnormal deviations in its SWIFT message traffic per country, financial institution and customer. Also, inaccurate SWIFT message parsing can have a detrimental effect on a correspondent bank’s ability to detect its respondent banks deviating from their anticipated activity profile which is usually captured when a new bank is on boarded by the correspondent. Deviations in historical activity at the SWIFT (BIC) level could also be an indication that a respondent bank “may” have been de-risked by another correspondent bank and consequently SWIFT traffic needs to be rerouted accordingly.
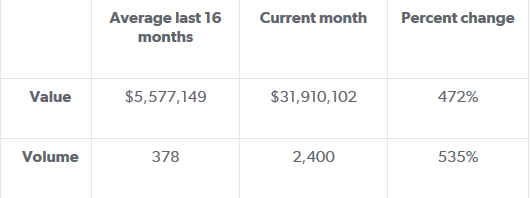
Another use case for deviations in historical activity is at the country level which could serve as an indication of geopolitical risks. For example, the diagram below represents the aggregation of Mongolian banks SWIFT message traffic over a 17 month period with a significant spike in activity when compared to its historical profile. From January 2013 through April 2014 the average value and volume for Mongolian banks has been $5.6M and 378. However, during the month of May 2015, the value and volume activity totaled $31M and 2,400 respectively. This deviation from the historical profile amounted to a percent change of 472% and 535% as shown in the table below. The spike in activity originating from the Mongolian banks coincided with new sanctions being imposed on Russia by the United States - and Mongolia happens to be in proximity to Russia.
While the above observation doesn’t imply causation, it does provide an interesting statistic for the financial institution’s compliance department to consider investigating. What is driving the sudden increase in SWIFT message traffic from the Mongolian banks and does it pose additional risks which can be mitigated? Conversely, if the spike in activity is innocuous because the financial institution recently expanded its footprint in the region then this explanation can be recorded and documented by the Compliance department to ensure senior management can explain this scenario to internal auditors and possibly regulators which alleviates the risk of the event being construed in a deleterious context.
Mongolian banks value and volume percent change from historical profile
Mongolian banks: SWIFT value & volume historical profile (17 months)
Transparency is the goal
The target state of any financial institution initiating or receiving SWIFT messages should be to have the greatest amount of transparency of their SWIFT traffic based on their risk appetite. Ideally, mapping SWIFT data to a transaction monitoring system (TMS) will allow the financial institution to accurately monitor deviations from historical profiles per country, SWIFT (BIC) and customer. Additionally, extracting country codes from the originating and beneficiary customer's address fields will allow for unique opportunities for custom data analytics and detection models such as customers banking outside of their jurisdiction.
These are some small improvements with low implementation costs which could make a big difference to how risky transactions and correspondent banks can be identified and managed. The question is, why aren't banks already making better use of the SWIFT data they have at their fingertips?
THE STRUGGLE FOR A HOLISTIC VIEW OF THE CUSTOMER AND THE RISK TO COMPLIANCE SYSTEMS
Most, if not all enterprises, would like to have a holistic view of their customers and this is especially true for Financial Institutions. However, the reality on the ground at some Financial Institutions seems to fall short of this goal for various reasons such as:
Issue
Most, if not all enterprises, would like to have a holistic view of their customers and this is especially true for financial institutions. However, the reality on the ground at some financial institutions seems to fall short of this goal for various reasons such as:
- Acquisitions and mergers with other companies
- Business lines operating as separate silos within the organization
- Incompatible technologies which is cost prohibitive to try to integrate in a meaningful way
- Data privacy laws and constraints of local jurisdictions where the customer was on-boarded
- Lack of an enterprise customer repository which stores all relevant customer information about the entity from all business lines
- Absence of standard rules of how the enterprise defines and can identify a customer across the institution
Enterprise Wide Initiative
Implementing a system which can provide a holistic view of the customer will most likely need the support of senior leadership in the institution to be successful as it will be an enterprise wide initiative with varying levels of complexity depending on the size, distribution and infrastructure of the organization. Additionally, the holistic view of the customer should be able to serve a wide audience within the organization which includes, but not limited to the following departments:
- Accounting
- Business lines
- Compliance
- Information Technology (IT)
- Legal
- Marketing
- Operations
- Risk
Financial Crimes Compliance
The lack of a holistic view of the customer is particularly evident when implementing financial crimes systems. When a financial institution implements a system to risk score its customers the organization will need to develop a plethora of rules which assign a score based on various attributes of the customer. For example, if “XYZ Inc.” was identified to be a Money Service Bureau (MSB) and one the beneficial owners of the business was identified as an inactive Politically Exposed Person (PEP) then this customer will end up with a particular score depending on the organization’s risk appetite.
Use Case
What if “XYZ Inc.” was a customer in four separate business line applications, with slightly different customer validation and on-boarding requirements, and the organization didn’t have an enterprise customer repository to realize that all of these instances of the customer were indeed the same entity? Then when it comes to down to risk scoring the customer the risk rating solution may need to ingest both records from each business line application to the financial crimes database because there are vital risk attributes in each application, but this will ultimately lead to customer fragmentation. One could argue that before the customer records are loaded to the financial crimes system there could be a process in place to combine, de-dupe or enhance the data to achieve a holistic view of the customer, at least, for Compliance purposes. The only downside to this approach is that it undermines the business line’s authority as the system with the most recent and accurate data of the customer for that product offering.
Current State
In the below diagram the customer "XYZ Inc." has been on-boarded or has accounts with four different business lines. However, the Financial Crimes Compliance department may be interested in specific risk attributes of the customer which are only relevant to each business line based on the type of products and services offered. Consequently, multiple versions of the same customer could be ingested and risk scored by the financial crimes system which has implications that are manifold.
- Risk scores could be inaccurate and understated due to a fragmented view of the customer
- The same customer with potentially different risk scores may have to be reviewed multiple times during the periodic review process which could drive up costs and inefficiencies
- Transaction monitoring and fraud investigations could also degrade in quality if the investigator does not have all of the relevant customer and transactional information in one consolidated alert
Target State
If, the financial institution is able to implement an Enterprise Know Your Customer (KYC) repository which can serve the needs of many different stakeholders then the Compliance department will undoubtedly be one of the major beneficiaries of this type of project.
Correspondent Banking: Risk rating the respondent bank's customers via watch lists
Correspondent banking could arguably be one of the most difficult business lines for AML (Anti-Money Laundering) suspicious activity systems to monitor, but are there any opportunities for improvement and increased sophistication? The fundamental conundrum for Compliance departments monitoring correspondent banking payment activity is that they must rely on the respondent bank's AML policies, procedures, controls and technology systems to identify suspicious activity and to take appropriate steps to mitigate the risks which could result in the respondent bank ending relationships with nefarious customers. In order to remain proactive banks providing access to the US financial markets via correspondent banking relationships should consider increasing the sophistication of how they detect suspicious activity based on what information is already contained in the wire payments and existing watch lists.
Correspondent banking could arguably be one of the most difficult business lines for AML (Anti-Money Laundering) suspicious activity systems to monitor, but are there any opportunities for improvement and increased sophistication? The fundamental conundrum for Compliance departments monitoring correspondent banking payment activity is that they must rely on the respondent bank's AML policies, procedures, controls and technology systems to identify suspicious activity and to take appropriate steps to mitigate the risks which could result in the respondent bank ending relationships with nefarious customers. In order to remain proactive banks providing access to the US financial markets via correspondent banking relationships should consider increasing the sophistication of how they detect suspicious activity based on what information is already contained in the wire payments and existing watch lists.
If, correspondent banks are monitoring their customer's customers then it requires several parsing algorithms to determine several key pieces of information such as:
Creating pseudo account numbers based on the originator and beneficiary names and addresses referenced in the wire payments.
Extracting country codes for the originator of the payments and, when available, for the beneficiary as well.
For example, if three different payments are processed by the correspondent bank and the originator of the payment has a similar name as shown in the Company Name column in the table below, then how can the system determine if the company in the wire payment is the same entity or not? The purpose of this article is not to delve into the wire payment parsing algorithms for account and country extraction, but the assumption is that a correspondent bank will have some type of system deriving this information before it makes it way to the suspicious activity monitoring system.
In general, most suspicious activity monitoring systems detect patterns based on the amount, velocity of activity and associated risks with the payment such as country risk. For example, if the company ABC LTD. sent 10 wire payments between the range of $50,000 and $250,000 to 5 different entities all located in high risk jurisdictions over a relatively short time period then this could be a scenario worthy of an investigation, if no other information was available on the originating customer. One key risk indicator which is missing from this scenario, but is part of most traditional suspicious activity monitoring systems, where the customer is on-boarded by the bank directly, is the customer risk rating. The correspondent bank only has information on the wire payment itself and has no information regarding the underlying originator and beneficiary of the payment. All payments are filtered through the bank’s Sanctions monitoring tool which will trigger alerts based on specific scenarios such as SDNs (Specially Designated Nationals), but most monitoring systems do not integrate the respondent bank’s customer risk because a lack of information.
However, watch lists could be leveraged to detect PEPs (Politically Exposed Persons) and entities associated with negative news which could range from fraud and embezzlement to possible links to terrorist groups. The watch list algorithm could be designed to assign a probability score to any potential matches in the wire payments against the watch lists. Then a bank AML/fraud investigator could review the wire payment to confirm if the name matched against the watch list is the same entity. After the confirmation from the investigator, any future payments by that entity would be under increased scrutiny and could be treated as a high risk customer which generally triggers alerts more often than low risk customers.
Negative news searches and PEP identification would be completed during most standard AML investigations if the entity triggered an alert, but the real value of this algorithm would be to identify high risk entities "below-the-line" or under the minimum alert score threshold which aren't triggering actual alerts.
Correspondent banks could also gather valuable information about their respondent banks by establishing ratios for banks with high concentrations of PEPs and/or entities linked to negative news relative to the bank’s size or payment activity. These metrics could be referenced during the correspondent bank’s de-risking process which may not always be intuitive because banks in low risk jurisdictions could be initiating high risk payments and conversely banks in high risk jurisdictions could be initiating lower risk payment activity.