MERCHANT-BASED MONEY LAUNDERING PART 3: THE MEDIUM IS THE METHOD
The previous editions of this series on merchant-based explored the many manifestations of the dark side of the terminal, including suspicious transactions merchants may see that could be tied to fraud groups and the risks tied to both closed loop and open loop prepaid cards.
To read the first story, covering “phantom shipments,” please click here. To read the second story on “prepaid gift card smurfing,” please click here.
Merchants can be involved with phantom shipments to move value across borders and cash can be anonymously loaded on prepaid gift cards through smurfing operations and used at US merchants to make sales revenue appear legitimate.
The rules and actions of the payment sector have direct implications on bank anti-money laundering programs.
How? Because while banks are technically not liable for the illicit actions of their customers’ customers – the customers of a merchant or payment processor – the bank is on the hook for properly inquiring about the risk of that customer base and compliance procedures, if any, of the merchants.
Editor's Note: This article originally appeared on the Association of Certified Financial Crime Specialists website on September 21, 2017.
The previous editions of this series on merchant-based explored the many manifestations of the dark side of the terminal, including suspicious transactions merchants may see that could be tied to fraud groups and the risks tied to both closed loop and open loop prepaid cards.
To read the first story, covering “phantom shipments,” please click here. To read the second story on “prepaid gift card smurfing,” please click here.
Merchants can be involved with phantom shipments to move value across borders and cash can be anonymously loaded on prepaid gift cards through smurfing operations and used at US merchants to make sales revenue appear legitimate.
The rules and actions of the payment sector have direct implications on bank anti-money laundering programs.
How? Because while banks are technically not liable for the illicit actions of their customers’ customers – the customers of a merchant or payment processor – the bank is on the hook for properly inquiring about the risk of that customer base and compliance procedures, if any, of the merchants.
At issue is that if a merchant or fraudulent site is later tied to a particular financial institution, and that bank never took the time to engage in the proper level of due diligence, creating a defend-able risk score and adequately tuning the transaction monitoring system, in the eyes of regulators, the bank could have a weak financial crime compliance program.
This article will focus on transaction laundering (TL), in its various forms, which I would argue is a subset of the broader problem of merchant-based money laundering (MBML). While it may appear that MBML is another form of trade-based money laundering (TBML), they are actually quite different for one reason.
To sum up a key mantra we will explain more on later, keep this in mind: the medium is the method.
In the 1960s, Marshall McLuhan coined the iconic phrase, “The medium is the message,” as he became the oracle of the electric age. But what did he really mean, when he said the medium is the message?
Fundamentally, McLuhan was pointing to the fact that how information is delivered to us through different mediums influence how we interpret the message itself and how it portrays social structures and our understanding of the world.
For instance, let’s take a lot at the tectonic shift in the human experience of conveying information when the world went from hand-writing and copying information to the printing press – which allowed for more wide-scale distribution of knowledge and ideas.
To be sure, the invention of the printing press was arguably one of the most important moments in human history and drastically influenced the development of the modern world.
Before the printing press, text would have to be copied manually by hand, which was inefficient, costly, and led to low rates of literacy.
Once printing was mechanized, it allowed for high rates of literacy and the rapid exchange of ideas. In that same vein, we think of money or value transfer as a medium which followed a similar evolution of the acoustic, written, mass production, and electric ages – going from a physical, spatially-limited form of value to a digital, internationally-fluid funding mechanism.
That idea is important to remember because one of the earliest adopters of new monetary technologies is the criminal element.
But let’s look for a moment at how different mediums affect our sensibilities to better understand the challenges to crafting criminal defenses against all the many ways money can move.
Just like television and radio has a completely different effect on our senses, laundering value through cash and merchant terminals leaves a completely different signature, something banks, regulators and investigators have to realize to balance the challenge of stopping criminal groups without creating customers friction and delays.
This is one of many fundamental struggles in the fight against money laundering, because many of the models we use today treat all forms of value transfer the same in terms of fighting financial crime and creating compliance programs, only looking at a few basic data points.
Additionally, regulators don’t want to stifle innovation, but they need to find ways to impose sensible regulations to keep pace with new mediums of money or value transfer.
Source: The Independent
The payments ecosystem as a new medium
As we said, however, in order to create current, relevant and agile ways to counter increasingly aggressive and creative organized criminal and terror groups, you need to understand how the United States structures its payments and settlements systems, and the panoply of players in the game, including banks, retailers, merchants, money services businesses, prepaid card providers, third-party payment processors and others.
The payment ecosystem in the US is complex and has a whole host of entities involved.
When a consumer makes a card purchase at a store or online, the payment flows through the payments ecosystem with the end goal of funding the merchant’s account, assuming the transaction is approved.
A consumer-initiated card purchase is commonly referred to as a “pull-payment” because the funds are pulled from the consumer’s account and deposited into the merchant’s account[1]. The three main steps of the payments process initiated by a consumer card purchase are:
- Authorization
- Funding
- Settlement
All of the above steps in the payments ecosystem involve various entities including, but not limited to the customer, merchant, gateway, processor, association and issuer.
[1] http://www.knowyourpayments.com/transaction-basics/
Source: Know Your Payments
What is transaction laundering?
Now that you have a better sense of the players in the payment chain and who does what, now we need to look at how criminals and fraudsters are trying to game the system.
Transaction laundering happens when a known merchant processes transactions for an undisclosed business.
This clandestine business is usually selling illegal products or services, and leverages the known merchant’s card processing accounts either through collusion or coercion – or simply because the merchant’s card processing systems are not tuned to be sensitive to financial crime and fraud red flags.
As a point of context, while banks, money services businesses and other entities considered a “financial institution” are subject to anti-fraud and anti-money laundering (AML) requirements, merchants typically are not, along with most third-party payment processors.
However, under current AML structures, some banks have foisted AML duties onto payment processors as a duty to continue to hold the account in the face of rampant de-risking in the financial sector, while third-party processors themselves may have to shoulder some counter-financial crime duties depending on how a prepaid payment chain is structured tied to recently-enacted rules.
Now, back to some of the red flags that can be employed by miscreant merchants.
The unknown businesses selling illegal products and services can disguise themselves in a number of ways, but here are some common examples described in a video by Dan Frechtling from G2 Web Services[1]:
- Cannabis sales intermingled with toy transactions
- Pirated movies appearing as software
- Prohibited injections posing as vitamin sales
Similar to red flags in the AML context, a guiding principle to determine if something is suspicious is if the transaction details don’t make sense for what the merchant should be doing or where they should be doing it.
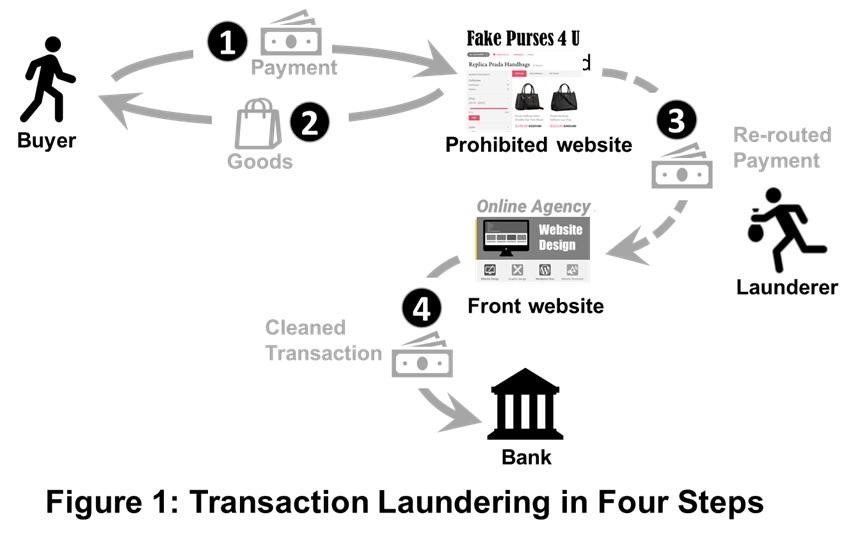
There are a number of challenges identifying transaction laundering, but one fundamental difficulty is that the complex payments ecosystem allow illicit transactions to enter through a variety of channels including, but not limited to: carts, gateways and virtual terminals. The below diagram illustrates a common example of transaction laundering:
[1] https://www.g2webservices.com/acquiring/g2-portfolio-protection/transaction-laundering/
Source: Transaction laundering in four steps https://www.g2webservices.com
But transaction laundering doesn’t end there.
The payments made for illicit products or services through the known merchant on behalf of the unknown business will be withdrawn from the known merchant’s bank account at some point in the future.
This is the touchpoint with the traditional banking world because the known merchant must have an account with a bank which receives the settled payments.
The ill-gotten gains can exit the merchant’s bank account through a number of methods, but the bank wouldn’t know of any suspicious activity and potential transaction laundering scenarios, unless the merchant acquirer informed the bank of the situation.
This obviously creates the need for a great deal of collaboration and information sharing between the merchant acquirer and the banks which hold the merchant accounts.
Who's responsible for transaction laundering?
Transaction laundering or credit card laundering is seen as a variation of money laundering by the U.S. Treasury’s Financial Crimes Enforcement Network (FinCEN) subject to suspicious activity reporting (SAR) requirements.
Transaction laundering violates several Federal Trade Commission, Telemarketing Sales, federal crime laws and some states have their own laws to address this problem. But that begs the question of which institution is supposed to file SARs?
Here is the answer, according to payment industry experts:
“Yet except for certain Money Services Businesses (“MSBs”), non-bank Third-Party Organizations such as ISOs/MSPs, Payment Facilitators/Payment Service Providers, data processors and network providers (collectively “TPOs”) generally are not subject to BSA requirements [highlighting mine]. Thus, it is the acquiring bank’s responsibility to (1) ensure that a TPO’s incident reporting and management program contains clearly documented processes and accountability for identifying, reporting, investigating, and escalating incidents of credit card laundering and other suspicious activity; and (2) monitor TPO compliance and processing information on an ongoing basis to ensure compliance with the acquirer’s SAR obligations.[1]”
As stated above, the answer is the acquiring bank.
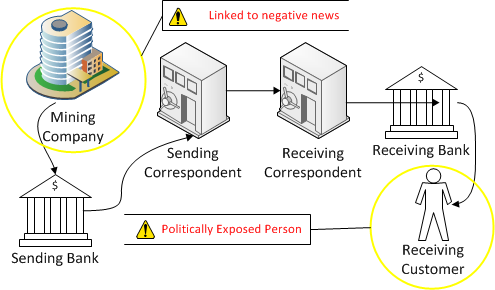
This seems oddly familiar because this situation sounds a lot like correspondent banking. In correspondent banking, the correspondent bank provides services to the respondent bank’s customers or the “customer’s customers.”
Essentially, the correspondent bank is relying on the strength of the respondent bank’s AML program, but ultimately the correspondent bank is held accountable for the payments processed by regulators in their local jurisdiction.
But the U.S. correspondent bank – the operation could also be, say, a New York branch of a foreign bank – processing the overarching transactions will be held accountable for properly risk-ranking the correspondent’s AML program and divining the overall risk score, something several foreign banks have been penalized for recently.
Similarly, the acquiring bank is relying on the payment processors to have adequate controls in place to detect transactions derived from illegal activity.
As regulatory actions focus more on payment processors, they could also face a round of de-risking practices, similar to what is occurring now in the correspondent banking space, by banks in the payments ecosystem.
Hence, it’s clearly in the best interest for payment processors to vigorously monitor their merchants’ activity and inform the acquiring bank of any instances of suspicious activity – lest they find they are tied to an illicit organized criminal group and become radioactive to global banks.
Beware cloaked illicit online gambling portals
Beyond shady and unscrupulous online business looking to dupe consumers and merchants, actors in the payment supply chain must also worry about illicit online gambling sites hiding their activities behind front company sites seeming to selling an array of innocuous items to not bring attention to themselves – in one recent case hiding behind a site selling household items.
On June 22, 2017, Reuters published an exclusive story which described an elaborate transaction laundering scheme used to circumvent local online gambling laws. Here is a short excerpt from the article below:
“The scheme found by Reuters involved websites which accepted payments for household items from a reporter but did not deliver any products. Instead, staff who answered helpdesk numbers on the sites said the outlets did not sell the product advertised, but that they were used to help process gambling payments, mostly for Americans.[2]”
This story was important because it was one of the first times a major publication detailed a transaction laundering scheme with real investigative reporting.
As these stories keep coming out from major publications and are linked to more heinous crimes, then it could help shine the spotlight on the risks of e-commerce and the connections to the criminal underworld.
Another challenge that the story indirectly highlighted was that even if merchant acquirers and payment processors could identify transaction laundering, they may not be able to identity the actual people behind the scheme due to the minimal customer due diligence being done in the industry.
Rather than a race to the top for compliance best practices in the traditional banking space, the payments industry has almost become a race to the bottom to offer no hassles and low fee structures in a highly competitive marketplace.
This can be illustrated by some entities in the payments ecosystem, as Dan Frechtling put it, offering “frictionless onboarding.”
Frictionless onboarding is not necessarily a bad thing in itself, but if a minuscule amount of customer information is required to open a merchant account and the information is not verified, then it becomes a problem.
Acquirers and payment service providers that wish to implement frictionless boarding without compromising their review policies may offer conditional approval followed by more stringent scrutiny in a post-boarding “containment” area.
This issue hits on a perennial debate in the compliance community: the potentially negligible value of an extensive customer review and risk assessment process versus defining risk by the transactions the customer actually engages, including going out of expected boundaries, or dealing with countries and entities historically considered high risk.
At the same time, the current momentum to more quickly create relationships that lead to new business creates a new quandary: How can you prevent the same bad actors from opening new fictitious websites and merchant accounts, if you don’t always know who’s behind the scheme?
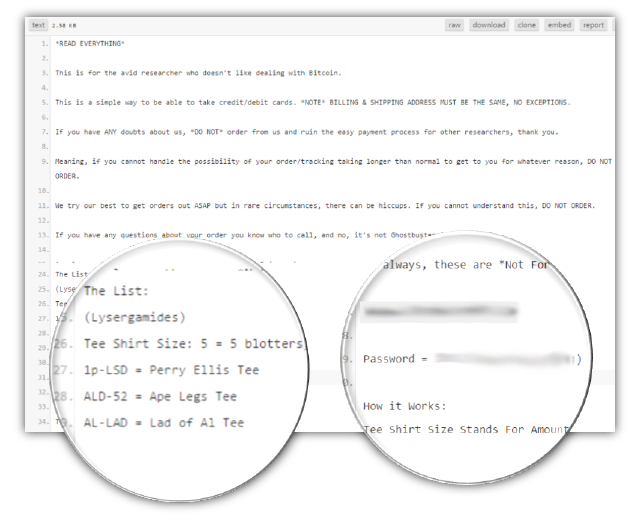
Don't die from a tie dye high
The risks of illicit groups working behind seemingly legitimate sites was brought into stark relief when investigators uncovered that a psychedelic t-shirt site, appropriately enough, was in actuality selling a tightly-controlled mind-altering drug
Lysergic acid diethylamide (LSD) was created by Albert Hofmann in Switzerland in 1938 from ergotamine, a chemical found in the fungus ergot. Dr. Hoffman accidently discovered the psychedelic effects of LSD in 1943.
The drug was experimented with for psychiatric reasons and the Central Intelligence Agency (CIA) even tested subjects to determine what type of mind control and wartime applications it may have.
In the 1960s, the counterculture movement popularized its mind-altering power and it was subsequently prohibited in both its use and distribution. Currently, LSD is listed as a Schedule I drug by the United States Controlled Substances Act, sitting alongside heroin, cocaine and, more controversially, marijuana.
LSD has been steeped in controversy where some leaders of the counterculture such as Timothy Leary touted its life-changing power and skeptics highlighting its dangers and links to accidental deaths caused by a profound state of altered consciousness.
For example, a student from Northern Illinois University was reported to have died as a result of LSD use when he fall out of a window[3].
Clearly, LSD is a very powerful drug, but unscrupulous merchants are still willing to sell it over the internet by disguising the real purpose of their websites.
Just imagine that if one was so inclined, you could find a website selling LSD, a schedule I drug, and order it with the click of a button and a credit card and have it delivered right to your door. Makes you wonder what else goes through the mail.
The below screenshot shows a real website appearing to sell tie dye t-shirts, but it was actually a front for a business selling LSD.
[1] https://www.g2webservices.com/blog/11865/acquirer-third-party-sar-obligations-transaction-laundering/
[2] https://www.reuters.com/article/us-gambling-usa-dummies-exclusive/exclusive-fake-online-stores-reveal-gamblers-shadow-banking-system-idUSKBN19D137
[3] https://www.inquisitr.com/2559752/lsd-becoming-popular-again-while-still-dangerous/
Source: G2 Web Services
The website itself has a number of red flags where the t-shirts are only offered in bulk and sizes are described in odd ways.
As well, the website had a checkout cart where if the credit card option was selected, it will send the visitor an email and redirect them to a separate website with a specific url link. This separate website was specifically designed to take credit card payments. One of the most interesting parts of this scheme was revealed below in a statement by the website operator:
“This is for the avid researcher who doesn’t like dealing with Bitcoin[1].”
[1] Source: https://www.g2webservices.com/blog/14723/real-life-launderers-tripping-transaction-laundering/
Source: G2 Web Services
This is actually quite a profound statement because it reveals the experience of the website operator conducting online drug deals was primarily with Bitcoin.
In other words, if a purchaser was so inclined to buy drugs online they could access the darknet via Tor and use Bitcoin to conduct their transactions almost completely anonymously as the only link to the illicit purchase would be the shipping address.
For online drug dealers to accept credit card payments, it shows they are serving a less technically savvy and larger segment of the drug market.
Anyone can make online purchases and the problem will only grow as people tell their friends about reliable drug dealing websites. Buyers don’t get the anonymity that the darknet and bitcoin offers, but it doesn’t seem to be slowing down the market.
Also, for the cautious and low value purchaser, they could load cash onto a prepaid card almost completely anonymously and would only be potentially linked to the illicit purchase based on the address provided.
But the United States in recent months have been targeting darknet drug bazaars and the virtual currency exchanges they are using, the key link to the real world and formal international financial system, in one case taking over a site undercover, watching and detailing the users and their online and fiscal exploits.
Drug dealer accepts credit card payments
One of the most brazen abuses of a merchant processing terminal was perpetrated by a local drug dealer in the United Kingdom.
The Police of Gloucestershire raided the home of Mark Slender on August 19, 2016 and seized cash, cocaine, cannabis, digital scales, and a chip’n’pin reader to take credit card payments[1]. The Police from Gloucestershire were shocked because they never saw a drug dealer take credit cards as a payment for drugs.
Slender even issued his customers receipts with the message, “Cheers, Gup.”
The Express article didn’t explain how Slender obtained access to a mobile chip’n’pin reader, but he could have been the one to open a merchant processing account on his own. This highlights one important point about the payment processing industry which is simply that there is no easy way to know, if merchants are selling illegal products or services through merchant processing terminals.
While most people buying illegal products would probably prefer some level of anonymity such as using cash in person or bitcoin on the darknet, some people may not even care or are so desperate to buy drugs that they use a credit card in the absence of cash.
Keep in mind that all many individuals need to process credit card transactions is an attachment to their smart phones and a bank account.
The publication reported that Slender was subject to a longer prison sentence due to previous drug dealing convictions. This raises an interesting point about the due diligence process for opening a merchant processing account and if a criminal background check would factor into the calculation of the fraud and money laundering risk profiles.
This is not to say that anyone with a criminal background should be prevented from opening a merchant account and processing credit cards, but they could pose additional risks to the institution.
Prohibiting new customers with criminal backgrounds may not be the answer at all, and could encourage more criminality, as such a practice, endorsed broadly, would push many suspicious actions underground, losing key intelligence federal investigators can use to take down larger criminal groups.
Ultimately, the customer with a criminal background poses additional fraud and money laundering risks, but they could be trying to rebuild their life and prohibiting them to open an account could prevent the reintegration into society as a whole and thus lead them back to the criminal life they may have been trying to escape.
Corporations are becoming more socially aware and active so this could be a situation where the institution absorbs the additional compliance costs of serving higher-risk customers for the greater good as opposed to simply de-risking whole categories of customers.
Don't wait for central registries and information sharing
While companies, retailers, processors, merchants and others try to juggle risk and find guys on an individual basis, countries as a whole must realize that larger organized crime groups and savvy fraudsters work internationally.
So the only way to stop them is forging stronger cross-border relationships with other firms and law enforcement because, currently, most countries don’t have central registries that detail high-risk or potentially criminal entities, currently the purview of third-party AML risk and list providers.
As well, while many large countries like the United States, United Kingdom and Europe have created county-wide financial intelligence units to store bank reports of potentially suspicious activity – and have attempted to better link these FIUs together – formatting, data privacy and resource constraints can conspire to limit their overall effectiveness.
Are the lack of central registries and information sharing between countries are a serious problem in the fight against money laundering and terrorist financing? Of course.
However, the problem with this argument is that it lessens the responsibility for each country, the country’s regulators and organizations operating within its jurisdiction to push the boundaries of what’s possible in the fight against financial crime.
There is a tremendous amount of external data sources that can be incorporated into AML programs to enhance detection capabilities including negative news, beneficial ownership and other open source data.
The advent of artificial intelligence, machine learning, and big data also open a whole host of new surveillance and analytic capabilities.
As with other forms of fraud, transaction laundering is more quickly exposed when firms use all their organizational eyes and ears. This includes sales representatives, underwriters, customer support staff and account monitors.
For example, G2 Web Services has observed adept organizations bring these professionals together to compare notes weekly or monthly, similar to the growing trend of convergence in the financial institution context where AML, fraud and cyber teams connect, cooperate and collaborate to better uncover illicit funds flowing through the bank and risks against the institution itself.
In the merchant-laundering arena, these notes may reveal conclusions about the same suspect business that were insignificant when singular but convincing when combined. In the event transaction laundering has occurred, cross-functional post mortems to look back for clues help banks avoid repeating mistakes.
[1] http://www.express.co.uk/news/uk/712043/Drug-dealer-uses-chip-pin-machine-take-twelve-thousand-pounds-customer-payments
Source: Collaboration across functions to spot transaction laundering, via G2.
Clearly, the payments industry doesn’t face the same type of AML and terrorist financing challenges as traditional banks.
However, this should not exempt the entities in the payments ecosystem from taking more proactive steps to identify and report suspicious activity. One of the challenges for organizations that have AML risk, but not to the extent of banks is that it's a slippery slope, and the cost of maintaining a comprehensive AML program potentially outweighs the perceived risks.
AML lite: One the periphery
What’s really needed for entities on the periphery of financial services such as attorneys, accountants, real estate brokers, merchant acquirers, payment processors, and FinTech firms is the idea of an AML lite program.
The traditional AML programs that have evolved in banks over the years tend to be top heavy, hierarchal, and slow to adapt to new trends.
While there will be significant challenges to come up with standards and solutions that smaller entities can adopt, additional AML coverage is needed across more industries to increase the identification of suspicious activity to help law enforcement to better put the pieces of the puzzle together.
Regulators also play a key role here.
These influential bodies sit in a tough spot because if they impose stricter AML regulations on entities that can’t adapt fast enough, then they could cause serious economic harm and put companies out of business.
On the other hand, if these entities, which sit on theperiphery of financial services are not required to comply with any rules, then it's likely they won’t do anything.
One strategy for regulators to continue to take, is to impose small incremental regulations for targeted industries and let the regulated institutions react and allow businesses to innovate and create services and solutions to meet those new requirements.
A recent example of this strategy was the action taken by FinCEN which renewed the “existing Geographic Targeting Orders (GTO) that temporarily require U.S. title insurance companies to identify the natural persons behind shell companies used to pay “all cash” for high-end residential real estate in six major metropolitan areas.”[1]
British Columbia implemented its own form of a geographic targeted order for any foreigners buying real estate in the Greater Vancouver Regional District (GVRD)[2].
Foreigner purchasers are supposed to pay an additional property transfer tax of 15% which was implemented as an effort to cool real estate market prices and to keep housing more affordable for the regular people of British Columbia.[3]
While it appears that British Columbia’s primary objective of the additional property transfer tax was to cool real estate market prices, it also likely reduced, to a certain degree, the amount of illicit funds flowing into the Vancouver real estate market.
Conclusion: A delicate balancing act for all involved
The fight against money laundering and terrorist financing is a delicate policy balancing act for regulators.
The AML industry is still in its infancy to a certain degree, because U.S. “The Patriot Act” was only signed into law on October 26, 2001 by President George W. Bush in response to the horrific 9/11 terror attacks.
That attack on the U.S. also pushed stronger global AML and counter-financing of terror standards, emboldening bodies like the Paris-based Financial Action Task Force (FATF), which is now the international standard-bearer of country-wide compliance structures.
So it seems Marshall McLuhan was right when he talked about the “Global Village,” because the world is smaller today and we are all more interconnected.
The technological advances of cars, trains, and buses allowed people to move farther away from the city into the suburbs. The internet and e-commerce allow us to buy almost anything, even LSD, with the click of a button.
The global village or the shrinking of the world has contributed to the difficulty in thwarting terror attacks because of the speed and variety of travel options available today. The evolution of how “value” is transferred is similar to transportation in the sense that value can move faster and in a wide variety of mediums today.
The car and airplane fundamentally restructured economies, cultures, and our perceptions of reality. Have we and society in general undergone a similar and perhaps more subtle transformation from the mushrooming mediums of value transfer?
No doubt, the human race has been shaped by these new ways to move money, just as we currently look for even newer, faster and cheaper ways to transact regionally and internationally. Just look at the advances of Bitcoin and its underlying technology the Blockchain.
But in step with the greater ability to move money quickly, easily and even, in some cases, nigh anonymously, detecting real instances of money laundering and terrorist financing in a reliable and automated fashion has grown even more incredibly complex.
Our understanding of how value is transferred and what are the potential exploits and weaknesses of each medium also must evolve to arrive at a more sophisticated approach to combat financial crime.
In other words, the medium is the method, requiring regulators, the private sector and watchdog bodies to craft new methods to better foster compliance, investigative and cooperative standards, best practices and methodologies to counter the entire spectrum of financial crime.
Such moves could formally or voluntarily nudge the payments sector to follow suit, making it harder for sham sites, fraudulent operators and illicit online casinos to engage in transaction laundering by arming merchants, processors, acquirers and others in the payments supply chain with the tools and resources to counter an array of criminal groups while supporting global commerce.
[1] https://www.fincen.gov/news/news-releases/fincen-renews-real-estate-geographic-targeting-orders-identify-high-end-cash
[2] http://www2.gov.bc.ca/gov/content/taxes/property-taxes/property-transfer-tax/understand/additional-property-transfer-tax#gvrd
[3] https://www.theguardian.com/world/2016/aug/02/vancouver-real-estate-foreign-house-buyers-tax
Data integrity can no longer be neglected in anti-money laundering (AML) programs
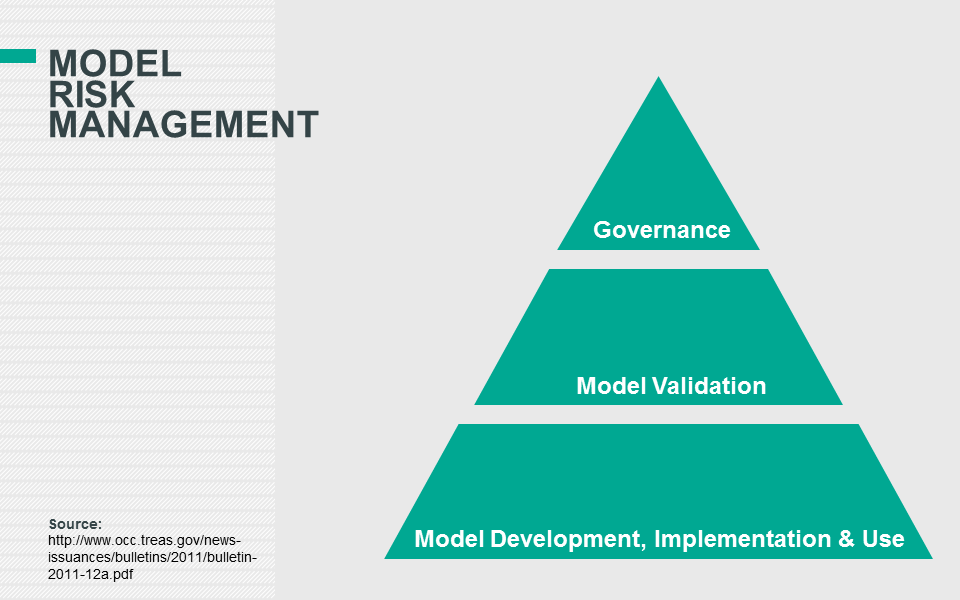
The New York State Department of Financial Services (NYDFS) risk based banking rule, went into effect on January 1, 2017 and will have a significant impact on the validation of financial institutions’ transaction monitoring and sanctions filtering systems. The final rule requires regulated institutions to annually certify that they have taken the necessary steps to ensure compliance.
Data integrity is particularly interesting because it arguably hasn’t been given the same emphasis as other components of an effective anti-money laundering (AML) program, such as a risk assessment.
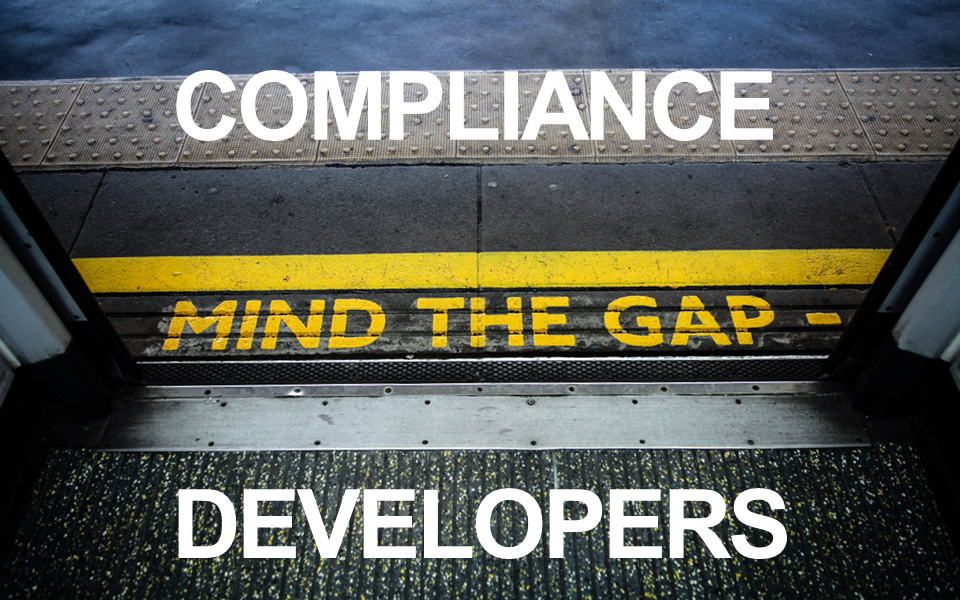
There has always been an interesting dynamic between the way compliance and technology departments interact with one another. This new rule will force institutions to trace the end-to-end flow of data into their compliance monitoring systems which could be a painful exercise. This exercise will demand the interaction between groups which may have stayed isolated in the past and it will require some parts of the organization to ask tough and uncomfortable questions to others. Clearly, gaps will be found and remediation projects will have to be launched to address those items.
Editor's Note: This article originally appeared on the Gresham Tech blog on May 15, 2017.
The New York State Department of Financial Services (NYDFS) risk based banking rule, went into effect on January 1, 2017 and will have a significant impact on the validation of financial institutions’ transaction monitoring and sanctions filtering systems. The final rule requires regulated institutions to annually certify that they have taken the necessary steps to ensure compliance.
Data integrity is particularly interesting because it arguably hasn’t been given the same emphasis as other components of an effective anti-money laundering (AML) program, such as a risk assessment.
There has always been an interesting dynamic between the way compliance and technology departments interact with one another. This new rule will force institutions to trace the end-to-end flow of data into their compliance monitoring systems which could be a painful exercise. This exercise will demand the interaction between groups which may have stayed isolated in the past and it will require some parts of the organization to ask tough and uncomfortable questions to others. Clearly, gaps will be found and remediation projects will have to be launched to address those items.
But does data integrity need to be such a painful endeavor? Could there be a better way to streamline the process - and even create value to the institution as a whole - increasing the enterprise value of data (EvD) by ensuring its integrity?
Can New York regulators really have a global impact?
Any financial institution which is regulated by the NYDFS should have already reviewed this rule in detail. Some have even suggested if financial institutions haven’t launched projects to ensure they can certify by April 15, 2018, then they are already behind.
What about financial institutions with no physical presence in the United States? Should these banks be paying close attention to this regulation? The answer is unequivocally – yes. First of all, if you read the rule it’s straight to the point and makes a lot of sense (it’s only five pages long). But it goes beyond just common sense and raising the standards and accountability for AML programs.
Imogen Nash, of Accuity, explored the global implications of NYDFS regulations, in a blog post back in August 2016, which are succinctly summarized below:
Ultimately, the argument is that as long as the U.S. dollar continues to hold its dominance among the world’s currencies then the reverberations of what the NYDFS requires will be felt across the globe.
What is data integrity?
Data integrity can be described as the accuracy and consistency of data throughout its entire lifecycle of being used by business or technical processes. The importance of accurate data in a financial institution can be easily demonstrated with a simple mortgage use case.
On day one, a customer is approved for a $1,000,000 mortgage with a monthly payment of $5,000. Let’s imagine that the loan system which approved that mortgage had a “bug” in it and on day thirty, the outstanding loan balance suddenly went to $0. Obviously, maintaining an accurate balance of outstanding loans is an important data integrity task for financial institutions.
Do banks really make these types of errors?
It wouldn’t be the norm, but there have been documented cases of unusual bank glitches, such as the Melbourne man whose account was mistakenly credited $123,456,789.
The miraculous $123M credit to a customer’s account is definitely an outlier because most core banking systems function fairly well. However, the reliability of a core banking system can’t necessarily be correlated to transaction monitoring and sanction screening systems.
The fundamental difference between the two types of systems is that the latter need to aggregate data from many different banking applications which are in scope for compliance monitoring. While each core banking application may function reliably well on its own - when all of these disparate banking systems are aggregated together into one compliance monitoring system, then various data integrity and quality issues arise.
But it’s not only the aggregation of disparate systems which is a problem, it’s the fact of how these systems are aggregated, which is like “fitting a square peg into a round hole.” Banks systems come in many shapes and sizes, but compliance monitoring systems are one-size-fits-all. Just imagine Shaquille O'Neal trying to fit into a toddler’s sneakers and then playing a full court basketball game. Some things just don’t fit and when things don’t fit, it could impact performance. It’s the same idea when forcing data into compliance monitoring systems.
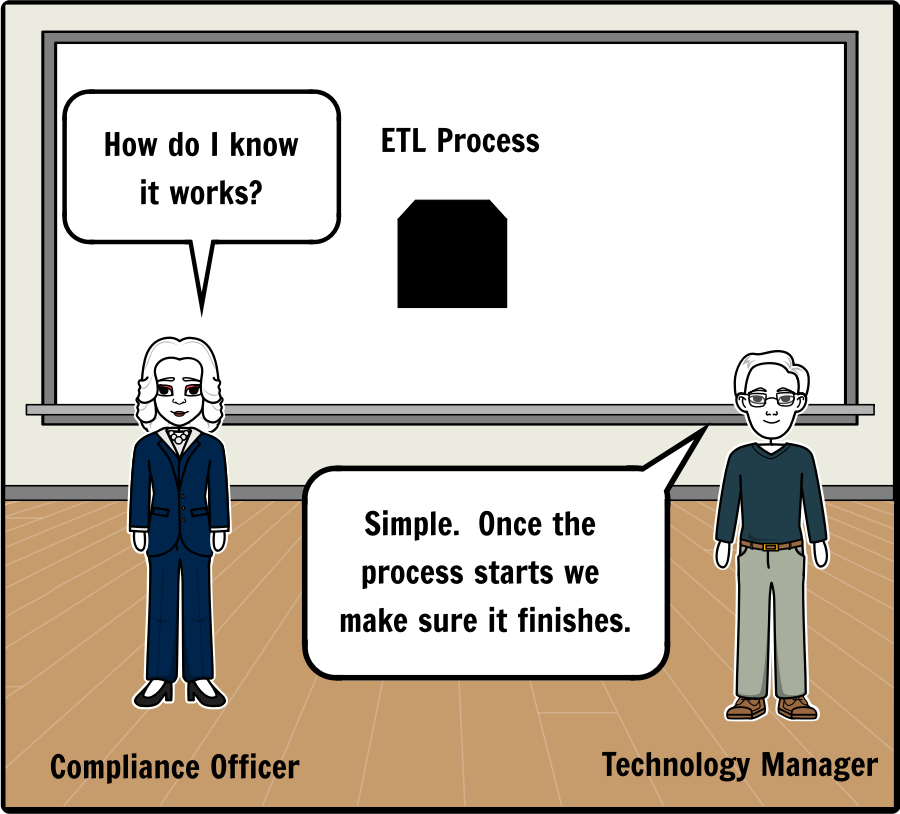
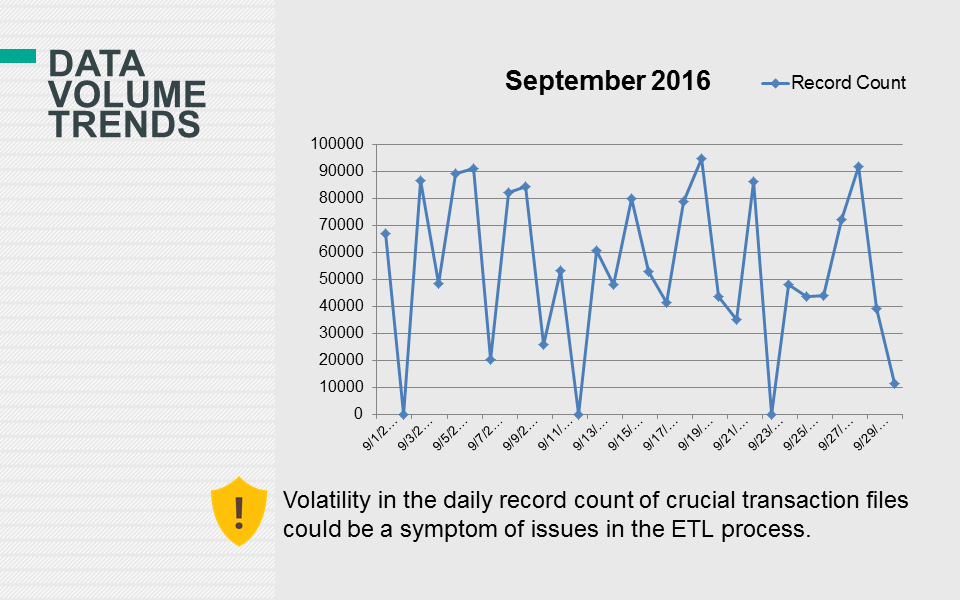
Why the extract, transform and load (ETL) process is a serious risk for compliance?
The process of moving data from the core banking applications to the transaction monitoring and sanctions screening systems presents several challenges and risks which should be validated on an ongoing basis. The process which moves data from one source system to another is generally referred to as the extract, transform and load (ETL) process. There are questions which arise at each stage of the ETL process such as:
- Was all of the data extracted properly?
- Was all of the data transformed from the source to the target system as designed?
- Was all of the data loaded from the source to the target system successfully?
Unless the a financial institution’s information technology (IT) department has already implemented data integrity and quality reports for their compliance partners, then the ETL process which supports financial crimes is nothing more than a “black box.” In other words, there would be no reliable way to determine the effectiveness of the data migration processes and controls without some level of reporting outside of IT.
Does the below interaction sound familiar?
The screenshot below highlights two requirements in the NYSDFS rule, but the key word to notice is “validation.” To validate the integrity, accuracy and quality of data is actually a significant effort because validation not only implies that a process is taking place, but it’s safe to assume that evidence will be requested to prove that the validation itself was complete and accurate. Since the rule is requiring the Board of Directors or Senior Officer(s) to certify that their institution is complying, then clearly senior management should require reporting around the ETL process or “black box” which feeds data into the transaction monitoring and sanctions screening systems.
2. validation of the integrity, accuracy and quality of data to ensure that accurate and complete data flows through the Transaction Monitoring and Filtering Program;
3. data extraction and loading processes to ensure a complete and accurate transfer of data from its source to automated monitoring and filtering systems, if automated systems are used;
Source: http://www.dfs.ny.gov/legal/regulations/adoptions/dfsp504t.pdf
It’s just data. No big deal right?
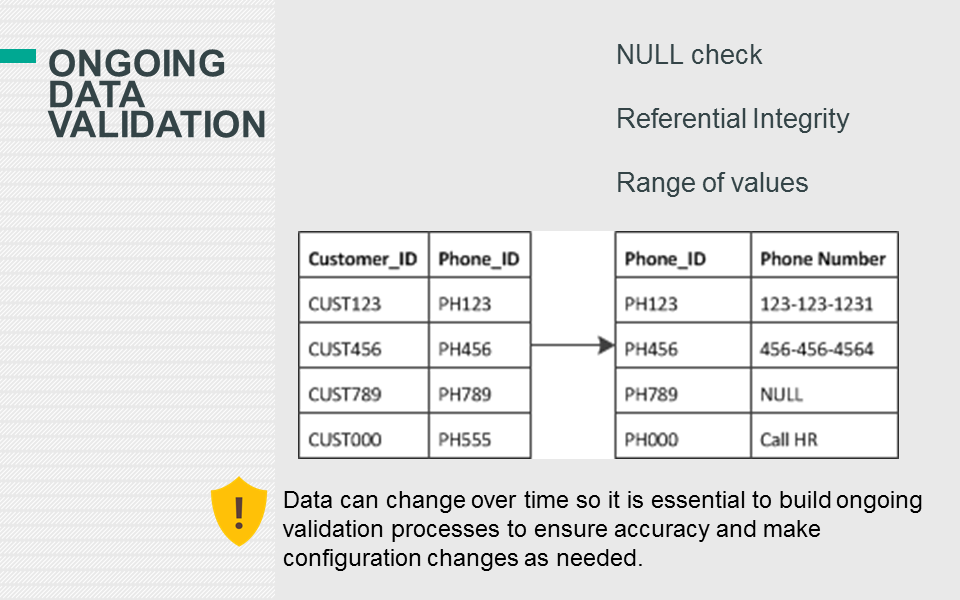
Implementing data integrity and quality checks is no simple feat and transaction monitoring and sanctions screening systems will have their own unique requirements. Transaction monitoring systems (TMS) generally require some level of transformation logic which categorizes various transaction types into groups, which are monitored by different AML models.
There are other common transformations which occur to support the TMS, such as converting foreign currencies to a base currency used for calculation logic. Obviously, you can’t sum transactions completed in Euros (€) and Japanese Yen (¥) together because the result would be erroneous.
These transformation rules are also susceptible to data integrity issues if the source systems make changes to their application without informing the owners of the TMS, who also may need to make changes to their own processes.
Why data integrity projects have failed in the past
Data integrity is not a new concept for those who work with AML systems. Actually, data integrity issues could potentially rank as one of the more popular responses by industry professionals for major impediments to the effectiveness of AML systems. Some banks are still using the data integrity processes they built internally or with third parties with varying degrees of success and sustainability.
One of the main issues is that many of these data integrity processes are built within the databases themselves or a dedicated data warehouse is constructed for this end. This may seem like a minor detail, but there are four ramifications:
- Exclusions: If, any exclusions are applied to customer, account or transaction data then it could be difficult to monitor what data is in scope and if it was extracted properly.
- Square peg in a round hole: The transform process is susceptible to significant data integrity issues because the source system is forced to conform to the compliance monitoring system’s data structure.
- Data validation: Generally, if a financial institution does have any data validation processes then they will performed in the “staging area” of the compliance monitoring system to ensure basic data integrity. Once the data validation process is moved forward to the “staging area”, then it’s essentially skipping steps one and two in the ETL process which can contribute to data integrity issues that are not identified. Another question which arises about the process is whether it’s ongoing or was performed one-time.
- Data lineage: When financial institutions use inflexible monitoring systems with strict data models it presents a challenge to data lineage. How can the financial institution trace back the data in the monitoring system to what’s in the source system? Even if they could follow the breadcrumbs; did the transform step in the ETL process manipulate the data so extensively that it’s become unrecognizable?
A path forward under the spotlight
Data integrity doesn’t seem to be going away anytime soon based on the fact that the NYDFS has just shined the spotlight on this issue. In our highly fragmented and compartmentalized modern world we may need to see the challenges we face through a new and objective lens.
Traditional approaches to data integrity projects have yielded limited quantifiable results in the past. Isn’t it about time to try a more flexible solution which can evolve seamlessly with the institution’s regulatory requirements and technological landscape?
Cost, flexibility and speed are three components of monitoring systems that financial institutions must manage effectively as regulatory requirements continue to expand due to growing threats such as cybersecurity. Data integrity is much broader than just compliance, but building the foundation to get it right for compliance monitoring can cross pollinate into other areas of the enterprise. Ultimately, data integrity can become a strategic business advantage when trying to enter new markets and launch new products.
[1] Onaran, Yalman. “Dollar Dominance Intact as U.S. Fines on Banks Raise Ire.” Bloomberg. 16 July 2014. http://www.bloomberg.com/news/articles/2014-07-15/dollar-dominance-intact-as-u-s-fines-on-banks-raise-ire
Web. 13 July 2016.
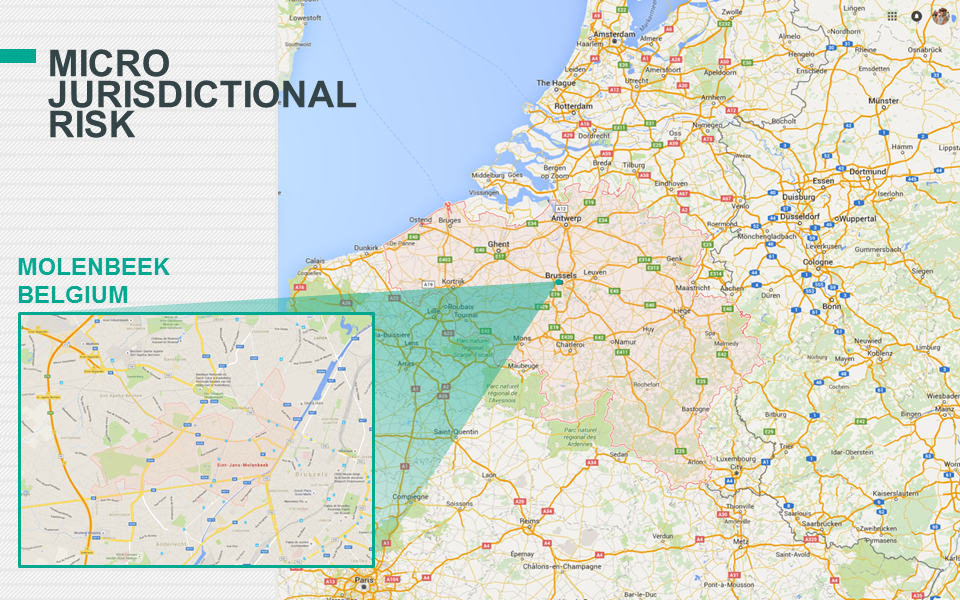
Micro-jurisdictional risk: One of AML’s missing links
High level jurisdiction risk assessments alone are often too broad in scope to include in anti-money laundering policies; Micro-jurisdictional risk analysis could help allay model bias.
- Some aspects of AML policies and procedures are in need of an overhaul, to capture variables important to making accurate analysis
- Low risk jurisdictions have high-risk neighbourhoods and, conversely, not all customers and transactions from high-risk jurisdictions warrant heightened scrutiny
- Financial institutions should go beyond existing AML guidelines and apply a more granular risk-based approach to geography to stay ahead of upcoming best practices
Editor's Note: This article originally appeared on The Asian Banker on May 9, 2017.
High level jurisdiction risk assessments alone are often too broad in scope to include in anti-money laundering policies; Micro-jurisdictional risk analysis could help allay model bias.
- Some aspects of AML policies and procedures are in need of an overhaul, to capture variables important to making accurate analysis
- Low risk jurisdictions have high-risk neighbourhoods and, conversely, not all customers and transactions from high-risk jurisdictions warrant heightened scrutiny
- Financial institutions should go beyond existing AML guidelines and apply a more granular risk-based approach to geography to stay ahead of upcoming best practices
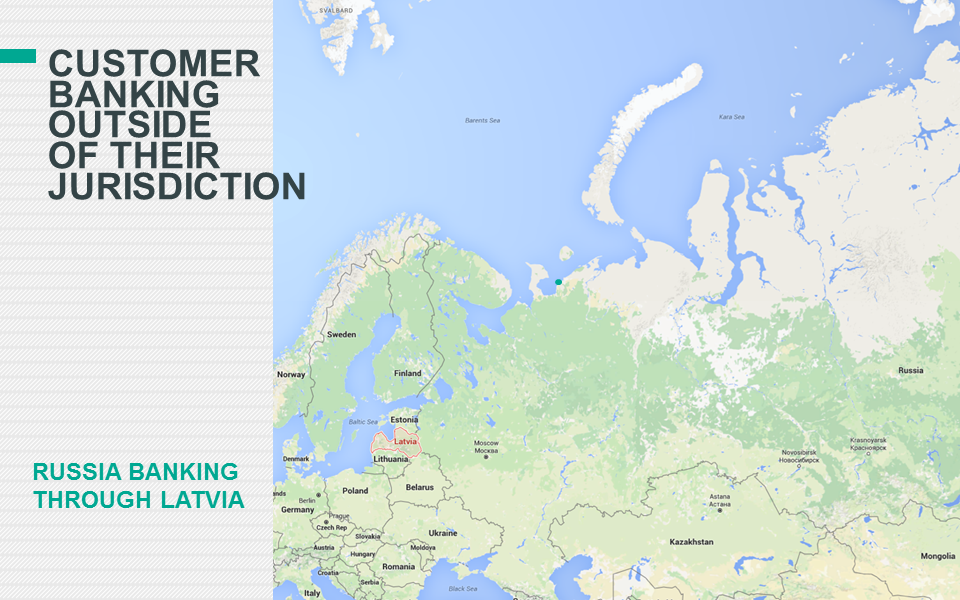
Financial institutions tend to build their anti-money laundering (AML) frameworks based on regulatory guidelines and commonly accepted industry standards. This can include jurisdiction risk, a common input banks use when evaluating customers and their transaction activity to determine degrees of AML risk, or to identify suspicious activity. Jurisdiction risks are based on a number of factors, including links to sanctions, terrorism, narcotics, corruption and other legislative and government deficiencies. The problem with attempting to include jurisdiction risk in AML policies is that it is simply too broad in scope, ranging from entire countries to subcomponents of cities, which lends such analysis to be either overemphasised or underemphasised as a data input.
As an example, there is strong evidence from the US that crime often occurs in High Intensity Drug Trafficking Areas (HIDTA), given the link between violent crime, competing drug distributors, and addicts looking to finance their next fix. HIDTA is an example of a high-risk micro-jurisdiction within the US, and banks may factor this into their lending decisions.
By contrast, foreign micro-jurisdictions have generally not been a component of AML programmes because of the large number of geographic areas which would need to be monitored on an ongoing basis, and the difficulty of defining how a standard of a high-risk micro-jurisdiction could apply across the globe. This leaves a gaping hole in the AML process, which severely limits its potential global impact.
As an example, while Belgium is generally considered to be a country with low credit, compliance, and traveller risk, it has also proven to be a breeding ground for Islamic extremism with a 2016 report by the International Centre for Counter Terrorism in The Hague noting that an estimated 13% of EU foreign fighters in Syria have roots in Belgium - the greatest number per capita of any country in the EU. An issue for Belgium is that information is not consistently shared between law enforcement agencies, making it easy for leads to fall through the cracks. Brussels has six police forces, each reporting to a different mayor. Given that rudimentary intelligence information is such a difficult process, what real chance do national or global law enforcement authorities realistically have to apply AML standards to the transfer of funds between terrorism suspects in Belgium, and between Belgium and destinations in the Middle East?
Other high-risk micro-jurisdictions have been tied to terrorism. Evidence has shown that funding for the 1998 U.S. embassy bombing in Nairobi was through a hawala office in its infamous Eastleigh neighbourhood, an enclave for Somali immigrants. Kenya is generally considered to be high for risk for travellers, with Eastleigh being at elevated risk due to violent crime and terrorist activity. Another example is El Salvador, which became the world’s most violent country in 2016 with its capital, San Salvador, becoming the world’s most homicidal city. San Salvador is clearly another high-risk micro-jurisdiction where law enforcement has itself become a victim of the drugs and gang war, with 49 police officers killed in 2015 alone. High murder rates can imply greater AML risk in specific geographic areas.
Even though a correlation can undoubtedly be made between high-crime neighbourhoods and money laundering, it is worth asking whether financial institutions should be responsible for applying a risk-based approach to these areas, as they would be required to do for other, non-high risk jurisdictions. Clearly there is great need for stripping bias from decision making to enable managers to make better decisions about whether, and how, to apply AML methodologies. Placing greater significance on managing jurisdiction risk would appear to be an important way to create greater awareness among investigators who review customers and their transactions.
However, imagine two publicly traded multinational companies conducting transactions with one another from high-risk jurisdictions. That should automatically be considered high-risk by virtue of geography, because the nature of risk depends on the entities involved, their reputation risk, history, and potential AML exposure. Should there turn out to be a strong correlation between customer risk ratings and jurisdiction risk, it could be a symptom that jurisdiction risk is being overemphasised. The same bias could apply to an institution’s transaction monitoring system, which may generate alerts in proportion to the jurisdiction’s risk level they originate from or terminate in.
Model biases can manifest themselves in any number of areas within an AML programme, including customer due diligence, transaction monitoring and sanctions. Focusing on micro-jurisdictions and other factors linked to transactions can allow for the recalibration of existing models to adapt a more granular risk-based approach. While it may seem like a daunting task to identify high-risk micro-jurisdictions, data is available and can be made useful more easily than many institutions may imagine, with the right approach. It is incumbent upon all financial institutions to go beyond existing AML regulatory guidelines to find the most effective approach to AML. Eventually, the regulations will catch up with emerging best practices.
Keith Furst is founder and financial crimes technology expert of Data Derivatives. Daniel Wagner is managing director of Risk Cooperative and co-author of the book “Global Risk Agility and Decision Making”. The views expressed herein are strictly of the authors.
BankThink De-risking shows failure of AML teams to innovate
Anti-money-laundering rules have always been a challenge in the financial services arena, with regulatory bodies demanding high standards of compliance and levying fines for noncompliance. Financial institutions have long struggled to meet those demands.
But the high regulatory burden of satisfying these rules is not an excuse for the current de-risking phenomenon, in which financial institutions are pulling out of regions and client relationships seen as carry money laundering risk, rather than face the costs and regulatory risk of maintaining those relationships. The conundrum associated with satisfying AML regulations has as much to do with a failure of imagination in efforts to follow the rules as it does with how onerous the regulatory requirements are.
Editor's Note: This article originally appeared on the American Banker on April 12, 2017.
Anti-money-laundering rules have always been a challenge in the financial services arena, with regulatory bodies demanding high standards of compliance and levying fines for noncompliance. Financial institutions have long struggled to meet those demands.
But the high regulatory burden of satisfying these rules is not an excuse for the current de-risking phenomenon, in which financial institutions are pulling out of regions and client relationships seen as carry money laundering risk, rather than face the costs and regulatory risk of maintaining those relationships. The conundrum associated with satisfying AML regulations has as much to do with a failure of imagination in efforts to follow the rules as it does with how onerous the regulatory requirements are.
Banks have a propensity to blame regulators and excessive compliance costs for their pulling out of business lines without necessarily trying to find a way to make it work. Compliance teams and other stakeholders have resisted being honest about the need to innovate. There has been a failure to experiment and an overreliance on “conventional” AML standard operating procedures.
Banks’ frustration with current industry tools, practices and standards have prompted a lobbying effort to call for reforms. A February 2017 report released by The Clearing House provided some excellent suggestions regarding information sharing, prioritization of AML/combating-the-financing-of-terrorism (AML/CFT) standards and beneficial ownership reporting requirements, among others. However, the report failed to acknowledge the possibility that existing regulations may be purposely broad and open to interpretation. The risk-based approach is a recurring theme in regulatory guidelines, but why must regulators have to clearly define priorities and standards for banks?
Banks can test hypotheses and discover new trends where guidelines may not exist, but the industry has discouraged deviations from accepted norms. The Clearing House report suggests that banks are afraid to innovate for fear of regulatory sanction. One can only wonder whether this is a palpable risk or a manufactured fiction spread by the AML industry. The explosion of funding in regtech startups by venture capital firms demonstrates that investors realize there is an opportunity to redefine the AML industry because it is evident that innovation will not come from within.
In fairness, the banks are not completely to blame, as the currently accepted tools to fight financial crime do not allow them to innovate. The conundrum associated with satisfying AML regulations has as much to do with a failure of imagination by a whole host of entities in the AML supply chain as with onerous regulatory requirements and compliance burdens. AML stakeholders — including banks, certification organizations, technology companies, regulators and the compliance community as a whole — have resisted being honest about the need to innovate.
To move the innovation needle forward, all parts of the supply chain will need to do their part. For the banks, part of the answer is to integrate AML/CTF with risk management processes more generally. This should not be a difficult task, particularly as so much of what banks do is transactional in nature. Nearly all banks have developed formal programs to manage transactional risk, and most of these are centralized so as to establish and maintain control over an entire network of operations. Transactional risk management is usually integrated with the credit risk management function, but larger banks tend to integrate transactional risk management into their overall risk management process.
Most banks take a comprehensive view of risk, but tend to differ in terms of how specific risks affect their risk-rating system. Many banks apply a single country rating to all types of exposures, while distinguishing between foreign and local currency funding. Formal exposure limits tend to be set annually and managed through the use of aggregate country exposures. Nearly all banks have developed formal programs to manage transactional risk, and most of these are centralized so as to establish and maintain control over an entire network of operations. Almost all banks assign formal country ratings, most of which cover a broad definition of risk. Ratings are typically assigned to all types of credit and investment risk, including local currency lending.
Transactional risk ratings establish a ceiling that also applies to credit risk ratings. Most banks do not generally have formal regional limits to lending, but some banks monitor exposures for a given region informally, and most have specific country limits. Many banks apply a single country rating to all types of exposure, while distinguishing between foreign and local currency funding. Formal exposure limits tend to be set annually and managed through the use of aggregate country exposures.
Few banks can say they have fully, effectively and efficiently integrated AML into the larger risk management process, or have linked AML with their country risk management programs. But such steps are needed, rather than merely continuing the de-risking blame game. The AML sphere is ripe for transformation on the part of all players in the supply, delivery and user chain. It may just be that the very regulatory oversight used to enforce compliance can be turned into the vehicle driving AML innovation.
The Other Elephant in the Room: Defeating False Negatives in AML Systems
False positives have a terrible reputation among anti-money laundering (AML) circles. As mentioned in my previous article on ending the false positive alerts plague, approximately 90-95 percent of alerts generated by Transaction Monitoring Systems (TMS) are false positives. So, why don’t we tighten our rule thresholds to let fewer alerts through?
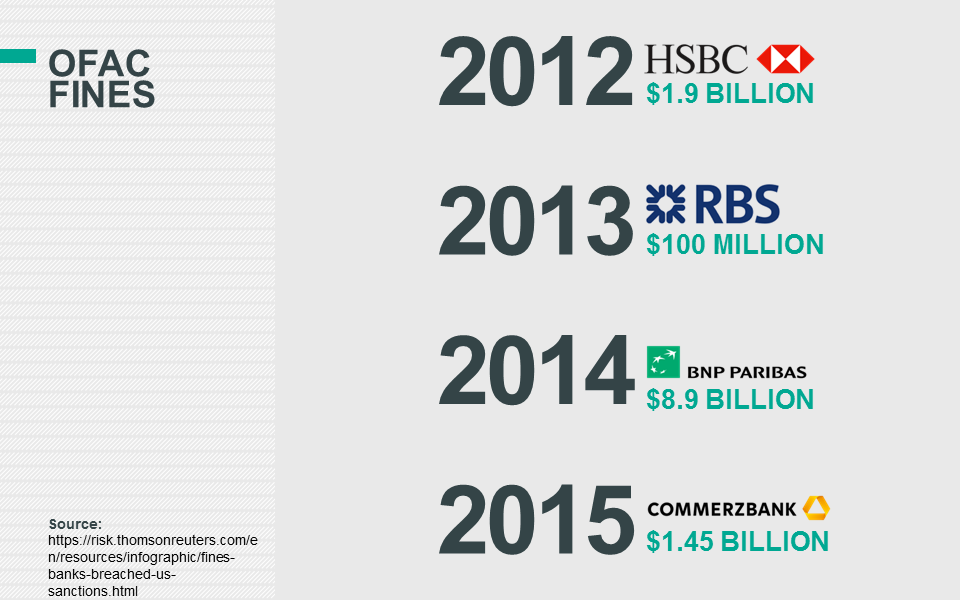
Unfortunately, tightening thresholds typically increases false negative alerts, which are real money laundering activities that the TMS didn’t catch. Though false positive alerts lead to high operational overhead, false negative alerts can cost you both in reputation and in major fines and penalties. As AML teams know, regulators have no qualms handing over hefty fines, which have risen considerably in the last decade.
Editor's Note: This article originally appeared on the DataVisor blog on March 5, 2017.
False positives have a terrible reputation among anti-money laundering (AML) circles. As mentioned in my previous article on ending the false positive alerts plague, approximately 90-95 percent of alerts generated by Transaction Monitoring Systems (TMS) are false positives. So, why don’t we tighten our rule thresholds to let fewer alerts through?
Unfortunately, tightening thresholds typically increases false negative alerts, which are real money laundering activities that the TMS didn’t catch. Though false positive alerts lead to high operational overhead, false negative alerts can cost you both in reputation and in major fines and penalties. As AML teams know, regulators have no qualms handing over hefty fines, which have risen considerably in the last decade.
Source: https://www.wsj.com/articles/no-more-regulatory-nice-guy-for-banks-1419957394
The fight against producing false negative alerts while trying to manage false positive alerts is like playing the world’s worst game of AML whack-a-mole. Just when you think that you’re fixing one of the problems, the other pops up with a vengeance. This begs the question: is it possible to reduce false negative alerts without increasing false positive alerts?
Is it a snake or an elephant? Seeing the whole picture
To answer this question, we first need to understand the root cause of false negative alerts. Think about the three general steps for a money laundering scheme: placement, layering, and integration. The big reason for false negative alerts is that most TMS only look at the symptoms of money laundering rather than the whole picture.
For example, an existing TMS might implement a rule that triggers if an account has multiple transactions close to, but less than, $10,000. A sophisticated money launderer knows about these rules, so they get around them by using stolen identities, multiple accounts, different transaction types, and low transaction amounts. Ideally, the TMS would not hard-code a cut-off threshold. Rather, a more sophisticated TMS would find the suspicious patterns to conclude that one person is behind the 100 accounts that are transferring money to each other.
Trying to catch money laundering with the current rudimentary rules systems we’re used to is similar to the parable of the blind men trying to identify an elephant. One blind man feels the trunk and thinks it’s a snake. Another feels a leg and thinks it’s a tree, and so on. Without a global picture of what’s going on, it’s impossible to spot the real money launderers (the “elephants”). The TMS is blind to many of the suspicious signals that money launderers unknowingly broadcast.
The Solution: global network detection with unsupervised machine learning (UML)
The solution to the false negative alerts problem is using unsupervised machine learning (UML) for global network detection. UML can view all of the activity at once, and in the context of all other accounts and activity. This is accomplished by linking accounts and activity together, which makes sense to humans but cannot be accomplished efficiently and comprehensively by existing TMS. By linking accounts, UML can detect hidden global networks of money laundering activity.
To understand what global network detection is, consider this example. Say Client A sends a payment to Client B, who then sends a payment to Client C. In current TMS, Client C’s demographic profile and other payment activity would not influence the rules contributing to an alert for Client A.
However, UML can uncover this undetected hidden link. Not only is Client B associated with Client C, but Client A is as well. Of course, this is an oversimplified example. Hidden links can be created with some combination of thousands of data fields to connect seemingly unrelated accounts and customers. The below image, which you may recognize from my first post, depicts customers which are linked based on shared demographic information such as an email address, physical address, phone number, internet protocol (IP) address and a common beneficiary.
The manual alerts queue will also change. Rather than looking at the account level, items in the review queue may contain multiple accounts, each with their own set of events. These accounts will be suspiciously linked in several ways. Ultimately, a human investigator will review what abnormal patterns were presented to them, but this approach saves the investigator time by not needing to manually comb through data and discover new patterns. Imagine the time savings if, instead of reviewing 100 alerts individually, you can review one hidden network with 100 linked accounts at once. Further, with all of the information presented upfront, there’s a much lower chance of accidentally missing something.
Ultimately, the major benefits of UML and global network detection make the decision clear. AML teams need to push themselves to embrace this new technology. By doing so, AML teams will:
- Have the sophistication required to see the bigger picture, taking hundreds to thousands of attributes at once
- Automatically adapt to new suspicious activity patterns and products launched
- Have more information about each account is given, reducing the time required to consolidate information for a case
- Triage many accounts and their coordinated activity at once, reducing the items in their queue
Existing TMS are too rudimentary to effectively catch money launderers, who are very good at quickly adapting and blending in. Money launderers have no choice but to be very careful and effective; the stakes are very high if they get caught. It’s up to the AML community to raise these stakes even more, and deter these money launderers from using our financial systems to funnel illicit funds.
Money Laundering in Canada 2016 Conference
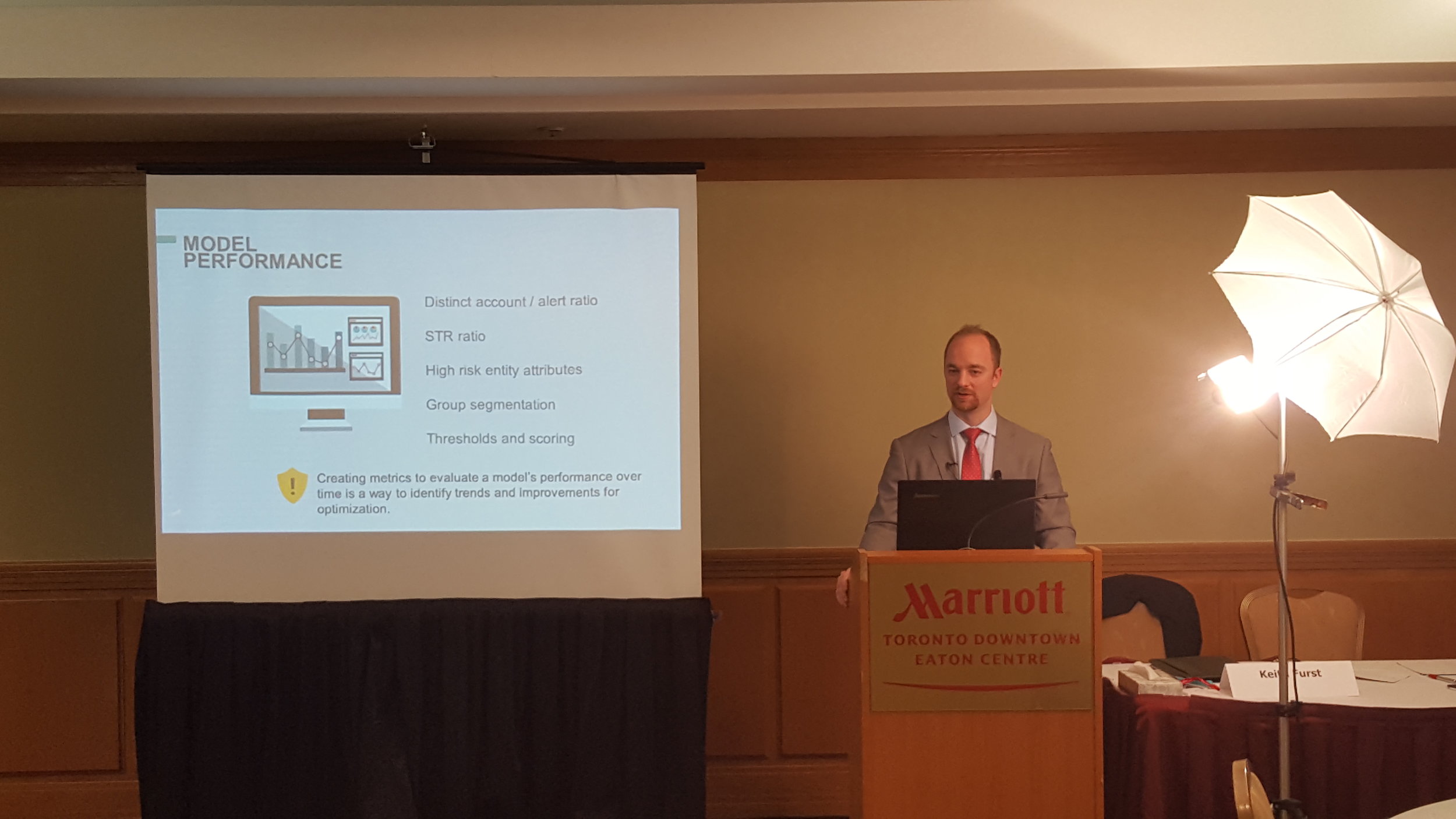
Data Derivatives was featured as one of the sponsors at the Money Laundering in Canada 2016 Conference.
Keith Furst giving a presentation on The SWIFT transparency problem and How to conduct an anti-money laundering (AML) system assessment. Both presentations were filmed and will be posted in the coming weeks.
The presentation from the event is below.
3 things we learned at our Fintech Talks - July Edition Dinner Event
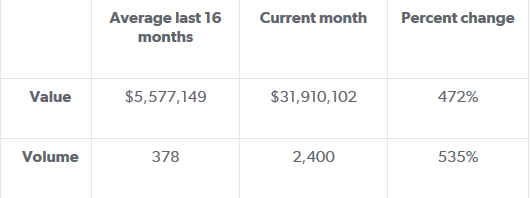
Last Thursday we had the privilege of hosting 30 senior banking executives at our quarterly FinTech Talks dinner event. The event theme was Trust, Transaction Monitoring and AML for financial messaging, and Keith Furst, a financial crime expert with experience at leading European and American financial institutions flew in from New York to headline the discussion.
Last Thursday we had the privilege of hosting 30 senior banking executives at our quarterly FinTech Talks dinner event. The event theme was Trust, Transaction Monitoring and AML for financial messaging, and Keith Furst, a financial crime expert with experience at leading European and American financial institutions flew in from New York to headline the discussion. Keith took our guests on a journey from past, to present and the possible future of AML mechanisms, correspondent banking, and explored the challenges associated with monitoring potentially fraudulent activity.
Click here to read about the full event details
Why Banks Must Evolve their AML Process to Manage Micro-Jurisdictional Risk
United States sanctions policies have evolved over the years, from country-wide embargos to more nuanced approaches targeting specific entities. According to Jacob J. Lew, Secretary of the Treasury, the sanctions implemented today are more focused on bad actors while trying to limit the negative externalities. Lew described his view on the traditional sanctions model at the Carnegie Endowment for International Peace which is eloquently summarized by this quote:
The Evolution of Sanctions
United States sanctions policies have evolved over the years, from country-wide embargos to more nuanced approaches targeting specific entities. According to Jacob J. Lew, Secretary of the Treasury, the sanctions implemented today are more focused on bad actors while trying to limit the negative externalities. Lew described his view on the traditional sanctions model at the Carnegie Endowment for International Peace which is eloquently summarized by this quote:
Lew went on to describe how the application of sanctions has evolved over the years, and through better financial intelligence, strategy, and design, the new model can home in directly on bad actors:
The Evolution of US Trade Sanctions
The diagram below illustrates the evolution of US Trade Sanctions. Longstanding sanctions would generally indicate a country-wide embargo, as is the case for Cuba and Iran. However, the Cuban and Iranian sanctions policies are currently in transition, as the traditional sanctions model is becoming deemphasized and would now only be used in extreme circumstances such as the case with North Korea. Sanctions imposed on African countries in 2005-2006 as highlighted in the diagram below were targeted sanctions based on human rights violations, concerns of regional stability or entities involved in undermining the democratic process.
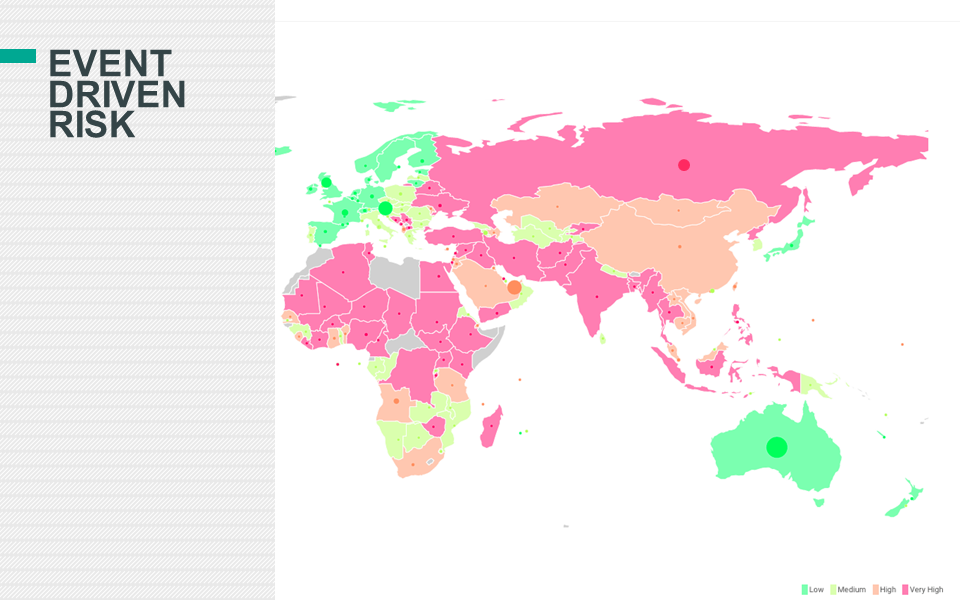
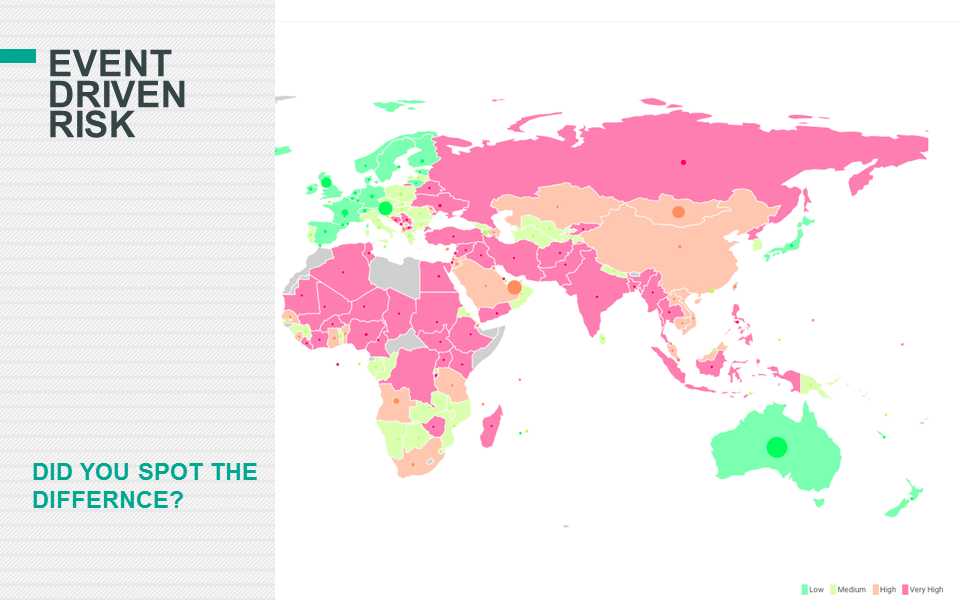
Jurisdictional Risk and AML Systems
The evolution of sanctions highlights how US regulators perceive risk. In the case of the African countries outlined above, sanctions were imposed to prevent the flow of money to the groups and individuals participating in local conflicts. The sanctions imposed were designed to prevent or at least slow down human rights violations. The question is, could this same perception of situational and jurisdictional risk be applied to anti-money laundering (AML) systems?
The Traditional AML Model
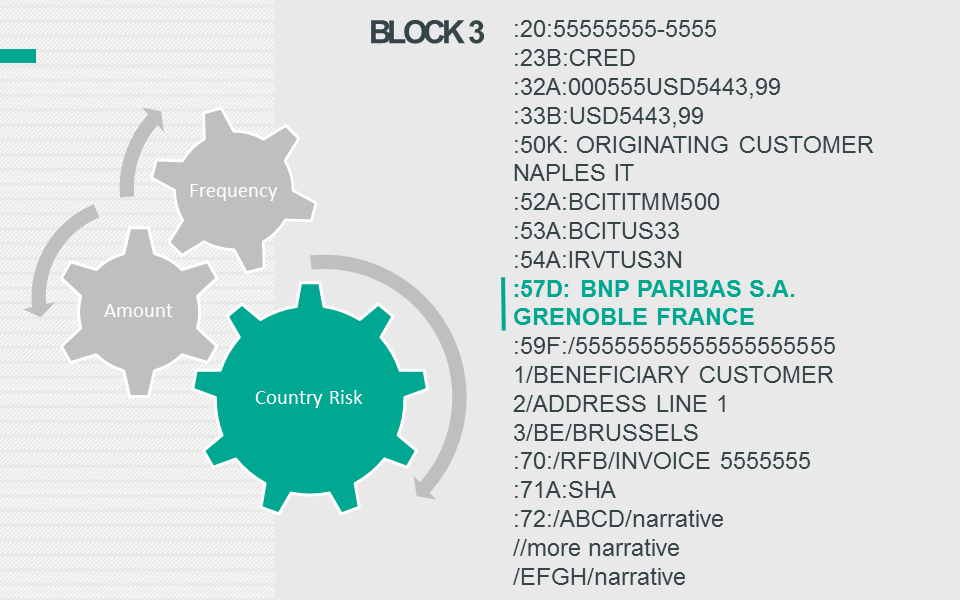
Cross-border transfers could be monitored based on a number of factors, but generally models are comprised of three main elements:
- Frequency: The number of transfers which occurred within a specific time period. Example: 3 transfers over a rolling 7 day time period.
- Amount: The value of each transfer. Example: A minimum threshold of X dollars could be configured in the monitoring system. Other elements would include round dollar amounts and amounts just below minimum reporting requirements.
- Jurisdictional risk: The risk level or score associated with each country. Example: Transfers flowing through high-risk jurisdictions would generally receive greater scrutiny than similar transactions which only flowed through low-risk jurisdictions based on the financial institution’s country risk ranking.
Financial Crimes Enforcement Network (FinCEN) Regulatory Guidance
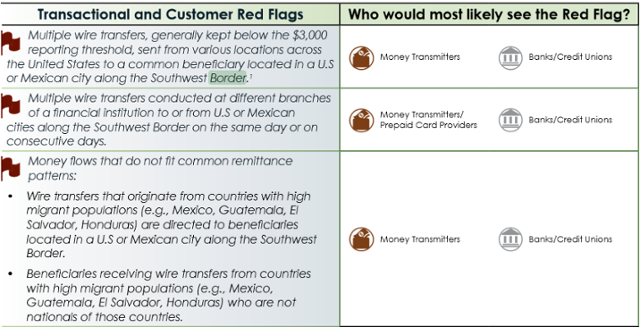
On September 11, 2014 Financial Crimes Enforcement Network (FinCEN) released an advisory guide called “Guidance on Recognizing Activity that May be Associated with Human Smuggling and Human Trafficking – Financial Red Flags” which was intended to help financial institutions identify human trafficking red flags. The interesting part is that FinCEN specifically identified both US and Mexican cities on the Southwest border as areas which require additional scrutiny as described in the transactional and customer red flags listed below:
Source: https://www.fincen.gov/statutes_regs/guidance/pdf/FIN-2014-A008.pdf
Micro-Jurisdictions: The Southwest Border
The image of the Southwest border below illustrates that there are multiple cities in the United States and Mexico that would fall within FinCEN’s advisory.
Micro-Jurisdictions: The Tri-Border Area (TBA)
The Tri-Border area is the region where the borders of Brazil, Argentina, and Paraguay meet, which has been known as a criminal haven for organized crime groups, terror groups and drug traffickers. In a report titled “TERRORIST AND ORGANIZED CRIME GROUPS IN THE TRI-BORDER AREA (TBA) OF SOUTH AMERICA” the author describes various conditions in the Tri-Border Area (TBA) that are very favorable to organized crime and terror groups in the below quote:
The three cities which are highlighted in the report are Ciudad de Este, Foz do Iguaçu and Puerto Iguazú because of their proximity to all three countries’ borders.
Challenges of natural language processing (NLP)
Traditional AML systems usually have functionality to support a list of country codes which can be segmented into categories such as low, medium, high, and very high risk. As a result, transactions which flow through higher risk jurisdictions should, in theory, receive greater scrutiny than lower risk transactions. Financial institutions usually store country codes in various systems based on the International Organization for Standardization (ISO) standard (ISO 3166-1) which can be represented in three formats:
- ISO 3166-1 alpha-2: Two-letter country codes.
- ISO 3166-1 alpha-3: Three-letter country codes.
- ISO 3166-1 numeric: Three-digit country codes.
The guidance issued by FinCEN adds another layer of complexity to AML systems because the red flags are not contained in a predefined list of country codes, but in a free text field such as a city, which creates a number of challenges.
The image below shows an address in Ciudad Juarez. Mexico and many financial institutions will have similar field definitions to capture addresses in various systems for client on-boarding or to facilitate a transaction. The only field which is based on a predefined list is the country code and sometimes the state/province, but most of the other fields are free text. However, some financial institutions will attempt to validate the address based on the information given, but not all organizations have the capacity to do so.
If most traditional AML models rely on country codes as a key attribute to determine suspicious activity, then how will a free text city be handled?
The Micro-Jurisdiction AML Model
Essentially, the FinCEN advisory is pointing to an extension of the traditional AML model where one of the additional attributes in the model would be a micro-jurisdiction. The main three components (Frequency, Amount and Jurisdictional risk) of the traditional AML model would still apply, but a fourth attribute would need to be added to the model and calibrated accordingly.
- Frequency: The number of transfers which occurred within a specific time period. Example: 3 transfers over a rolling 7 day time period.
- Amount: The value of each transfer. Example: A minimum threshold of X dollars could be configured in the monitoring system. Other elements would include round dollar amounts and amounts just below minimum reporting requirements.
- Jurisdictional risk: The risk level or score associated with each country. Example: Transfers flowing through high-risk jurisdictions would generally receive greater scrutiny than similar transactions which only flowed through low-risk jurisdictions based on the financial institution’s country risk ranking.
- Micro-Jurisdictional risk: The risk level or score associated with specific towns, zip codes or cities. Example: Transfers flowing through high-risk micro-jurisdictions would generally receive greater scrutiny than a similar transaction which only flowed through low-risk micro-jurisdictions based on the financial institution’s risk ranking.
The Implications of Micro-Jurisdictional Risk
If regulators continue to issue guidance which highlights specific geographic areas as part of a money laundering typology, then traditional AML systems must evolve or engage third party vendors which can process large volumes of data quickly, and without impacting the daily operations of the financial institution’s overall AML program. Another question which comes to mind is to what extent financial institutions should be proactive?
Should financial institutions begin to gather their own intelligence to identify potential high-risk micro-jurisdictions or should they wait for advisories from their respective regulators? The amount of intelligence gathered could be relative to the financial institution’s risk appetite and geographic footprint.
Traditional AML systems may not be the optimal solution to process large volumes of data to extract towns, zip codes and cities from free text fields. Hence, using a third party solution based on the latest advances in computing technology that can cleanse, prepare and risk rate the data before it is sent to the traditional AML systems would be beneficial to financial institutions.
Identifying and monitoring high-risk micro-jurisdictions could extend a financial institution’s AML program’s sophistication by focusing on the more granular attributes of transactional activity and consequently pushing the risk-based approach to new horizons.
TRUST, TRANSACTION MONITORING AND AML FOR SWIFT MESSAGING
As regulatory and compliance controls become increasingly strict, how confident can you be that you are doing enough to spot and prevent risky SWIFT transactions and money laundering attempts?
As regulatory and compliance controls become increasingly strict, how confident can you be that you are doing enough to spot and prevent risky SWIFT transactions and money laundering attempts?
Join us on July 14th as we discuss Trust, Transaction Monitoring, and AML for SWIFT messaging.
The challenges and benefits of mapping SWIFT messages to your Transaction Monitoring System (TMS)
The Regulatory landscape and SWIFT messages
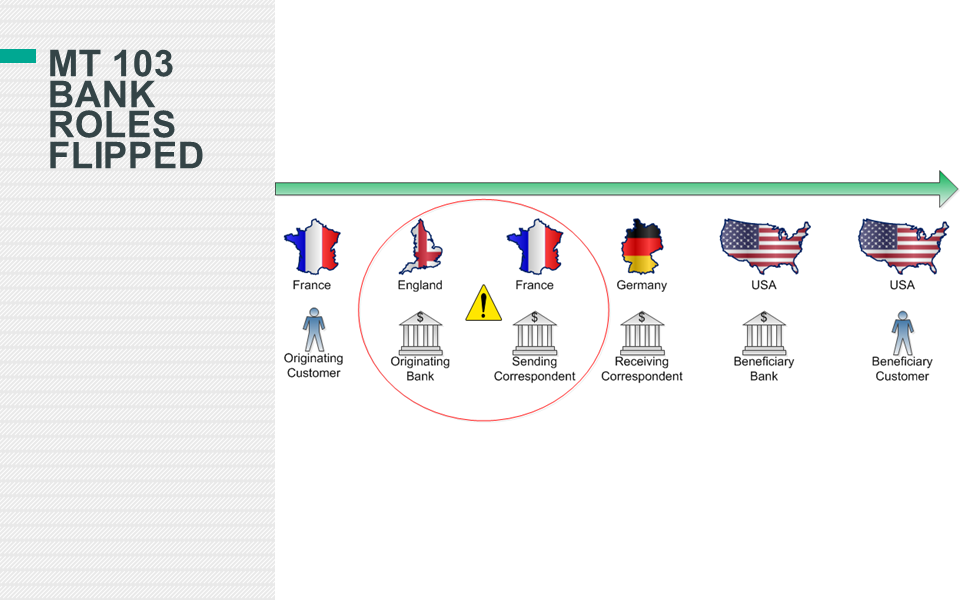
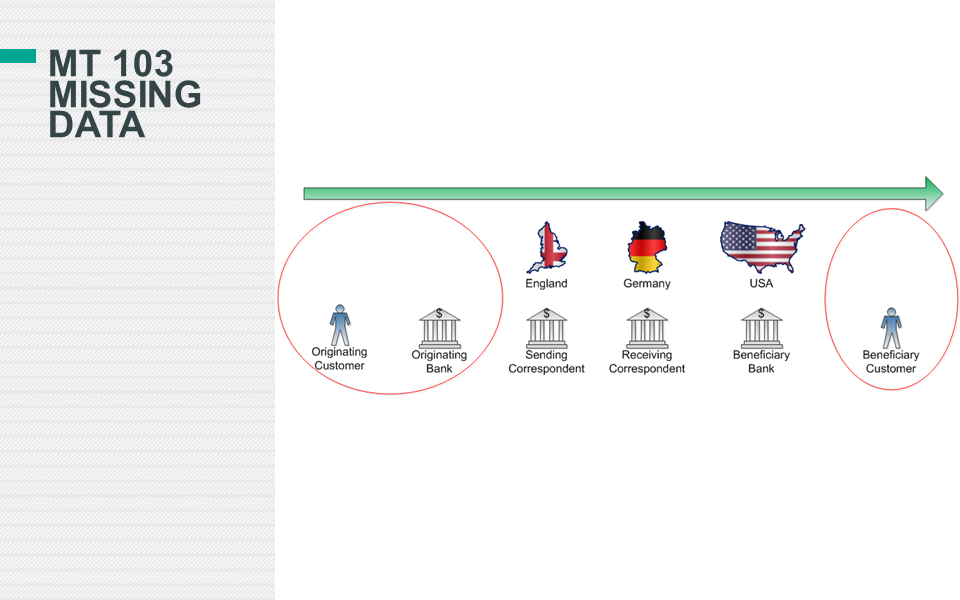
Cross-border payments have been a central theme in recent regulatory actions where regulators levied record breaking fines against financial institutions that failed to comply with Bank Secrecy Act / anti-money laundering (BSA / AML) regulations. The Society for Worldwide Interbank Financial Telecommunications (SWIFT) is, in some sense, at the heart of these violations because it is one of the major facilitators of global money transfers which have come under increased scrutiny.
Editor's Note: This article originally appeared on the Gresham Tech blog on February 18, 2016.
The Regulatory landscape and SWIFT messages
Cross-border payments have been a central theme in recent regulatory actions where regulators levied record breaking fines against financial institutions that failed to comply with Bank Secrecy Act / anti-money laundering (BSA / AML) regulations. The Society for Worldwide Interbank Financial Telecommunications (SWIFT) is, in some sense, at the heart of these violations because it is one of the major facilitators of global money transfers which have come under increased scrutiny.
The enforcement actions came about for a range of reasons, but a general assertion made by regulators in many of the major violations was that banks had inadequate Bank Secrecy Act / anti-money laundering (BSA / AML) programs. A press release issued by the Department of Justice (DOJ) illustrates how regulators perceive failures of anti-money laundering (AML) programs to be a major infraction by financial institutions.
“A four-count felony criminal information was filed today in the District of Columbia charging Commerzbank with knowingly and willfully conspiring to commit violations of IEEPA and Commerz New York with three violations of the BSA for willfully failing to have an effective anti-money laundering (AML) program, willfully failing to conduct due diligence on its foreign correspondent accounts, and willfully failing to file suspicious activity reports. Assuming the bank’s continued compliance with the deferred prosecution agreement, the government has agreed to defer prosecution for a period of three years, after which time, the government would seek to dismiss the charges.”
What does an effective anti-money laundering (AML) program mean?
Effective anti-money laundering programs involve a wide variety of activities, resources, leadership and technology, but for the purpose of this article, the focus will be to discuss what improvements can be made when mapping SWIFT messages to transaction monitoring systems (TMS) and the common pitfalls and data quality issues which arise from this endeavor.
Transaction monitoring systems (TMS) are software applications which have been specifically designed to assist financial institutions to satisfy their BSA / AML requirements by leveraging pattern recognition algorithms that detect activity abnormalities and other money laundering typologies. Financial institutions involved in cross-border payments may be members of SWIFT, and consequently some of the institution’s SWIFT traffic may be subject to BSA / AML monitoring requirements based on their local jurisdiction's rules and regulations.
Mapping SWIFT messages to transaction monitoring systems (TMS)
Data mapping can be a difficult task in itself based on the wide variety of source system applications and middleware a financial institution can be supporting, but some transactional activity is more complex than others to map based on its structure and the number of data elements involved. This is particularly evident when a financial institution maps SWIFT messages to its transaction monitoring system (TMS). Some of the challenges stem from, but are not limited to the following:
- Number of entities involved in the message
- Financial institutions, large corporations, businesses and individuals
- Different SWIFT message types and formats to facilitate various banking functions such as trade finance, foreign exchange, securities settlements, cross border payments, etc.
- Periodic updates and changes to SWIFT message formats and validations
- Free text format of certain fields
- Options to represent the same data differently in the same field
- Large reference data sets required to extract the necessary data for Compliance
- Development of in-house message parsing tools subject to limitations and inaccuracies
- Inflexible vendor solutions that can parse messages, but not to the extent needed for transaction monitoring systems (TMS)
- Knowledge gap between personnel in payment operations and the individuals implementing the transaction monitoring systems (TMS)
Levels of complexity
Financial institutions can vary quite significantly in terms of how sophisticated their monitoring of SWIFT messages is, but all are subject to a certain level of inaccuracy. The table below illustrates three levels of complexity for the mapping of SWIFT messages to a transaction monitoring system (TMS).
Correspondent banks and other financial institutions
Financial institutions which support correspondent banking will be inclined to implement the intermediate and advanced levels of SWIFT message mapping, especially in the more developed countries, because of the amount of scrutiny placed on banks from regulators for engaging in this business. Correspondent banking is considered very risky because the correspondent bank providing clearing services to their respondent banks are predominantly relying on their respondents to have an adequate BSA / AML program. However, respondent banks generally will abide by the rules and regulations of their host country which could differ from the correspondent’s and the perception and risk appetite of each institution can also vary widely.
Financial institutions which do not provide correspondent banking services can still benefit significantly from implementing the intermediate and advanced level of SWIFT data mapping because of the increased detection capabilities the data offers.
Common inaccuracies
If a SWIFT message is not parsed correctly it could misrepresent which role each financial institution played in the message such as the originating bank, sending correspondent, receiving correspondent, beneficiary bank or other type of intermediary.
1. Bank roles and countries in the message flipped
The diagram below represents a MT103 SWIFT message where there are four banks and two customers involved in the message. However, the originating and sending correspondent bank roles have been flipped and the actual sending correspondent bank is represented as the originating bank, and the originating bank appears as the correspondent.
2. Wrong bank and country represented in the message
In the second example in the diagram below, the financial institutions are not flipped, but the originating bank is actually represented incorrectly. The originating bank appears to be located in Mexico, but the bank is actually located in France.
3. Key risk attributes missed in basic mapping model
Another more insidious example that represents the limitations and lack of transparency of mapping SWIFT messages according to the basic level of complexity is shown in the diagram below. First, the originating bank and its country code is unable to be identified because the basic parsing model expects a SWIFT (BIC) to be supplied, but the originating bank’s name and address was populated instead. Second, the basic parsing model is not sophisticated enough to extract the country codes from the originating and beneficiary customer address fields and consequently this key information is blank.
If the mapping model was able to extract the country code from the originating and beneficiary customer address fields, then the Compliance department would have the opportunity to create a new detection scenario such as the customer banking outside of their jurisdiction. While there are instances where an entity can have a legitimate reason to bank outside of its jurisdiction it is an important risk indicator that can be leveraged and help the institution fine tune its system by implementing a more targeted and risk based approach.
Why does accuracy matter?
While on an individual transaction level the inaccuracies described above may appear to be trivial, on a macro scale it could severely undermine a financial institution’s ability to monitor abnormal deviations in its SWIFT message traffic per country, financial institution and customer. Also, inaccurate SWIFT message parsing can have a detrimental effect on a correspondent bank’s ability to detect its respondent banks deviating from their anticipated activity profile which is usually captured when a new bank is on boarded by the correspondent. Deviations in historical activity at the SWIFT (BIC) level could also be an indication that a respondent bank “may” have been de-risked by another correspondent bank and consequently SWIFT traffic needs to be rerouted accordingly.
Another use case for deviations in historical activity is at the country level which could serve as an indication of geopolitical risks. For example, the diagram below represents the aggregation of Mongolian banks SWIFT message traffic over a 17 month period with a significant spike in activity when compared to its historical profile. From January 2013 through April 2014 the average value and volume for Mongolian banks has been $5.6M and 378. However, during the month of May 2015, the value and volume activity totaled $31M and 2,400 respectively. This deviation from the historical profile amounted to a percent change of 472% and 535% as shown in the table below. The spike in activity originating from the Mongolian banks coincided with new sanctions being imposed on Russia by the United States - and Mongolia happens to be in proximity to Russia.
While the above observation doesn’t imply causation, it does provide an interesting statistic for the financial institution’s compliance department to consider investigating. What is driving the sudden increase in SWIFT message traffic from the Mongolian banks and does it pose additional risks which can be mitigated? Conversely, if the spike in activity is innocuous because the financial institution recently expanded its footprint in the region then this explanation can be recorded and documented by the Compliance department to ensure senior management can explain this scenario to internal auditors and possibly regulators which alleviates the risk of the event being construed in a deleterious context.
Mongolian banks value and volume percent change from historical profile
Mongolian banks: SWIFT value & volume historical profile (17 months)
Transparency is the goal
The target state of any financial institution initiating or receiving SWIFT messages should be to have the greatest amount of transparency of their SWIFT traffic based on their risk appetite. Ideally, mapping SWIFT data to a transaction monitoring system (TMS) will allow the financial institution to accurately monitor deviations from historical profiles per country, SWIFT (BIC) and customer. Additionally, extracting country codes from the originating and beneficiary customer's address fields will allow for unique opportunities for custom data analytics and detection models such as customers banking outside of their jurisdiction.
These are some small improvements with low implementation costs which could make a big difference to how risky transactions and correspondent banks can be identified and managed. The question is, why aren't banks already making better use of the SWIFT data they have at their fingertips?
Correspondent Banking: Risk rating the respondent bank's customers via watch lists
Correspondent banking could arguably be one of the most difficult business lines for AML (Anti-Money Laundering) suspicious activity systems to monitor, but are there any opportunities for improvement and increased sophistication? The fundamental conundrum for Compliance departments monitoring correspondent banking payment activity is that they must rely on the respondent bank's AML policies, procedures, controls and technology systems to identify suspicious activity and to take appropriate steps to mitigate the risks which could result in the respondent bank ending relationships with nefarious customers. In order to remain proactive banks providing access to the US financial markets via correspondent banking relationships should consider increasing the sophistication of how they detect suspicious activity based on what information is already contained in the wire payments and existing watch lists.
Correspondent banking could arguably be one of the most difficult business lines for AML (Anti-Money Laundering) suspicious activity systems to monitor, but are there any opportunities for improvement and increased sophistication? The fundamental conundrum for Compliance departments monitoring correspondent banking payment activity is that they must rely on the respondent bank's AML policies, procedures, controls and technology systems to identify suspicious activity and to take appropriate steps to mitigate the risks which could result in the respondent bank ending relationships with nefarious customers. In order to remain proactive banks providing access to the US financial markets via correspondent banking relationships should consider increasing the sophistication of how they detect suspicious activity based on what information is already contained in the wire payments and existing watch lists.
If, correspondent banks are monitoring their customer's customers then it requires several parsing algorithms to determine several key pieces of information such as:
Creating pseudo account numbers based on the originator and beneficiary names and addresses referenced in the wire payments.
Extracting country codes for the originator of the payments and, when available, for the beneficiary as well.
For example, if three different payments are processed by the correspondent bank and the originator of the payment has a similar name as shown in the Company Name column in the table below, then how can the system determine if the company in the wire payment is the same entity or not? The purpose of this article is not to delve into the wire payment parsing algorithms for account and country extraction, but the assumption is that a correspondent bank will have some type of system deriving this information before it makes it way to the suspicious activity monitoring system.
In general, most suspicious activity monitoring systems detect patterns based on the amount, velocity of activity and associated risks with the payment such as country risk. For example, if the company ABC LTD. sent 10 wire payments between the range of $50,000 and $250,000 to 5 different entities all located in high risk jurisdictions over a relatively short time period then this could be a scenario worthy of an investigation, if no other information was available on the originating customer. One key risk indicator which is missing from this scenario, but is part of most traditional suspicious activity monitoring systems, where the customer is on-boarded by the bank directly, is the customer risk rating. The correspondent bank only has information on the wire payment itself and has no information regarding the underlying originator and beneficiary of the payment. All payments are filtered through the bank’s Sanctions monitoring tool which will trigger alerts based on specific scenarios such as SDNs (Specially Designated Nationals), but most monitoring systems do not integrate the respondent bank’s customer risk because a lack of information.
However, watch lists could be leveraged to detect PEPs (Politically Exposed Persons) and entities associated with negative news which could range from fraud and embezzlement to possible links to terrorist groups. The watch list algorithm could be designed to assign a probability score to any potential matches in the wire payments against the watch lists. Then a bank AML/fraud investigator could review the wire payment to confirm if the name matched against the watch list is the same entity. After the confirmation from the investigator, any future payments by that entity would be under increased scrutiny and could be treated as a high risk customer which generally triggers alerts more often than low risk customers.
Negative news searches and PEP identification would be completed during most standard AML investigations if the entity triggered an alert, but the real value of this algorithm would be to identify high risk entities "below-the-line" or under the minimum alert score threshold which aren't triggering actual alerts.
Correspondent banks could also gather valuable information about their respondent banks by establishing ratios for banks with high concentrations of PEPs and/or entities linked to negative news relative to the bank’s size or payment activity. These metrics could be referenced during the correspondent bank’s de-risking process which may not always be intuitive because banks in low risk jurisdictions could be initiating high risk payments and conversely banks in high risk jurisdictions could be initiating lower risk payment activity.